Multi-perimeter firewall in the cloud
Patent No. US10574482 (titled "Multi-perimeter firewall in the cloud") on Apr 7, 2016. The application was issued on Feb 25, 2020.
What is this patent about?
'482 is related to the field of network security, specifically to systems and methods for providing multi-perimeter firewalls within a global virtual network (GVN). The background acknowledges the limitations of traditional WAN optimization and VPN technologies in addressing latency and security issues, especially in scenarios with geographically distributed users and cloud-based services. The patent aims to improve network performance and security by strategically positioning distributed firewalls at multiple perimeters in the cloud.
The underlying idea behind '482 is to create a multi-layered firewall system within a GVN that leverages the cloud's scalability and distributed nature. Instead of relying on a single firewall at the network edge, the invention proposes placing multiple firewalls at different points within the GVN. This allows for a more comprehensive and adaptable security posture, where different types of inspection (e.g., stateful packet inspection and deep packet inspection) can be applied at different stages of traffic flow.
The claims of '482 focus on a multi-perimeter firewall system located in a cloud and forming part of a global virtual network. The system includes an egress ingress point device, first and second access point servers, and an endpoint device. A first perimeter firewall performs stateful packet inspection (SPI) at the first access point server, while a second perimeter firewall performs deep packet inspection (DPI) on a cloned copy of traffic at the second access point server, preventing malicious traffic from reaching the endpoint device.
In practice, the system operates by routing network traffic through the GVN, where it encounters the first firewall performing stateful packet inspection. This firewall quickly examines packet headers to identify and block known threats. Traffic that passes this initial filter is then forwarded to the second firewall, which performs deep packet inspection on a copy of the traffic. This more thorough inspection analyzes the packet payload for sophisticated threats, without impacting the speed of the main traffic flow.
This approach differs from traditional firewalls by distributing the security functions across multiple points in the network and by using a combination of SPI and DPI. The use of a cloned traffic stream for DPI is a key differentiator, as it allows for in-depth analysis without introducing latency. Furthermore, the system is designed to be scalable, leveraging cloud resources to handle varying traffic loads and attack volumes, and the firewalls can share threat intelligence to improve overall security.
How does this patent fit in bigger picture?
Technical Landscape
In the mid-2010s when ’482 was filed, global network security was typically implemented using hardware-based firewalls situated at the physical perimeter of a local area network. At a time when systems commonly relied on point-to-point encrypted tunnels or expensive dedicated circuits like MPLS to maintain quality of service between geographic branches, software-defined architectures were beginning to address the latency issues inherent in backhauling traffic to a central gateway. Hardware and software constraints made it non-trivial to maintain high-performance security filtering across distributed cloud environments without introducing significant delays that impacted the user experience for real-time applications.
Prosecution Position
The examiner allowed the application because the prior art did not disclose the specific combination of a multi-perimeter cloud firewall system where a first firewall performs stateful packet inspection and a second firewall performs deep packet inspection on a cloned copy of the network traffic. While existing technologies used multiple firewalls in series or performed various types of inspections, the examiner determined that the specific sequence of filtering traffic through these distinct inspection methods—specifically utilizing a cloned copy for the deep packet analysis within a global virtual network—was not anticipated or rendered obvious by previous systems.
Claims
This patent contains 26 claims, with claims 1 and 13 being independent. The independent claims are directed to a multi-perimeter firewall system located in a cloud. The dependent claims generally elaborate on the features and configurations of the firewall system described in the independent claims.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
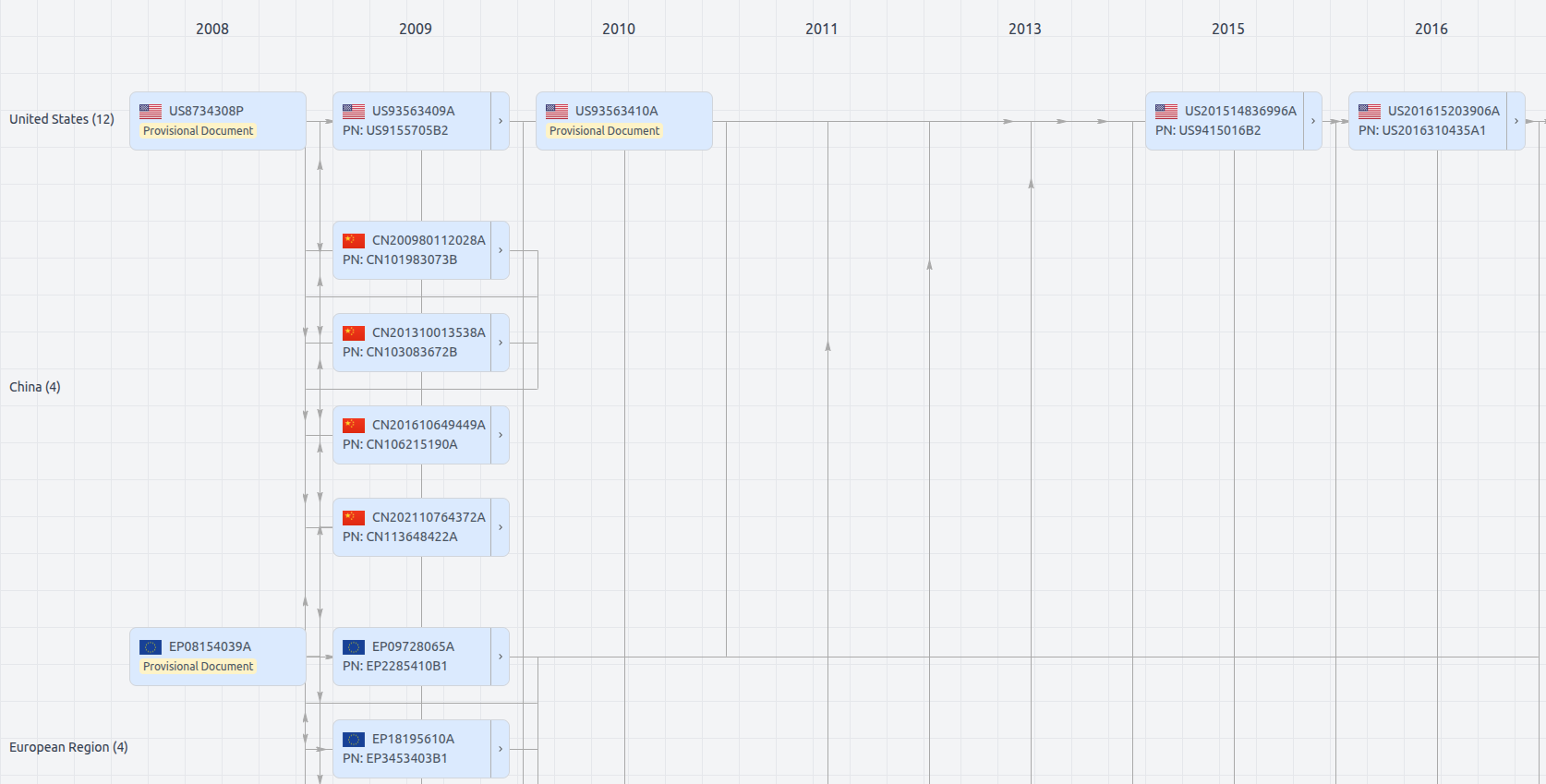
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Get instant alerts for new documents
US10574482
- Application Number
- US15563261A
- Filing Date
- Apr 7, 2016
- Publication Date
- Feb 25, 2020
- External Links
- Slate, USPTO, Google Patents