Systems And Methods Of Device Based Customer Authentication And Authorization
Patent No. US10904234 (titled "Systems And Methods Of Device Based Customer Authentication And Authorization") was filed by Privakey Inc on Jul 8, 2019.
What is this patent about?
’234 is related to the field of Internet-centric authentication and, more specifically, to systems and methods for authorizing the initiation of remote services by mobile device users. The background acknowledges the vulnerabilities of traditional username/password schemes and the limited adoption of existing multi-factor authentication methods due to complexity and cost. The patent aims to provide a more secure and user-friendly authentication process for accessing online services.
The underlying idea behind ’234 is to leverage a mobile device as a secure authentication token. This involves creating an authentication token on the mobile device, storing the private key portion securely on the device, and only transmitting the public key portion to an authorization service. When a user attempts to initiate a remote service, the authorization service sends a challenge to the mobile device, which validates the user's credentials and responds, enabling the authorization service to initiate the requested service.
The claims of ’234 focus on a system comprising a processor and storage devices at an authorization service (AS). The claims cover the AS receiving only the public key portion of an authentication token from a mobile device, receiving a remote service identifier and challenge information from a remote service server, transmitting challenge information to the user's mobile device, receiving messages from the mobile device, validating these messages using the stored public key portion, and, if validated, initiating the remote service. The claims also cover a non-transitory machine-readable storage device encoded with program code that, when executed by a processor of a mobile device, performs a method of creating and using the authentication token.
In practice, the invention works by embedding authorization service code within a remote service application on a mobile device. This code creates an authentication token specific to the user's credentials and the authorization service code itself. The private key portion is stored securely on the device, while the public key portion is sent to the authorization service. When a remote service initiation is attempted, the authorization service sends challenge information to the mobile device, prompting the user to validate their credentials. If validated, a message is sent back to the authorization service, enabling the remote service to be initiated.
This approach differs from prior solutions by providing a more secure and convenient authentication method. By storing the private key portion securely on the mobile device and only transmitting the public key portion, the system reduces the risk of credential theft. Furthermore, the use of a challenge-response mechanism ensures that the user is actively involved in the authentication process, preventing unauthorized access. The invention also allows for a more seamless user experience by integrating the authentication process directly into the remote service application.
How does this patent fit in bigger picture?
Technical landscape at the time
In the mid-2010s when ’234 was filed, at a time when multi-factor authentication was gaining traction, systems commonly relied on SMS-based one-time passwords or hardware tokens for enhanced security. However, hardware or software constraints made the implementation of user-friendly and cost-effective multi-factor authentication solutions non-trivial, especially for Internet-centric applications.
Novelty and Inventive Step
The examiner approved the application because the claims are directed to a system for authorizing the initiation of remote services for mobile device users. The system includes an authorization service with a processor and storage devices. The storage device stores public key portions of authentication tokens for mobile device users and remote service identifiers. The authorization service processor receives only public key portions of authentication tokens created on mobile devices. When a remote service is initiated, the program code receives a remote service identifier and challenge information from a remote service server, transmits challenge information to the user's mobile device, validates messages from the user's mobile device using the stored public key portion of the authentication token, and initiates the remote service if validation is successful. The examiner stated that prior art references do not teach or suggest the specific combination of elements and steps recited in the claims.
Claims
There are 20 claims in total. Claims 1, 10, and 16 are independent. The independent claims generally focus on systems and methods for authorizing remote services using authentication tokens and challenge information. The dependent claims generally add detail and limitations to the independent claims, further defining the components, steps, and functionalities of the claimed inventions.
Key Claim Terms New
Definitions of key terms used in the patent claims.
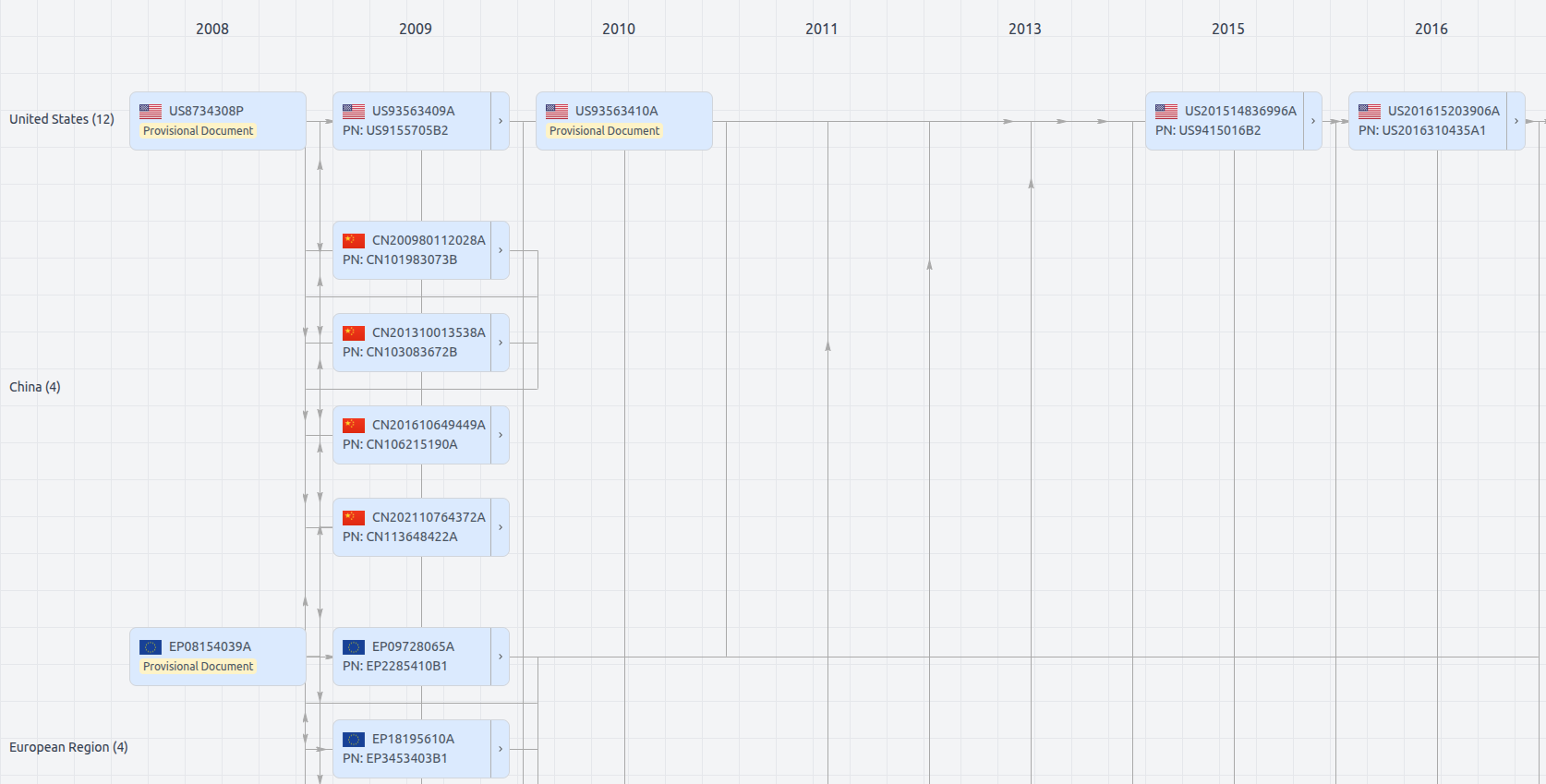
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US10904234
- Application Number
- US16505353
- Filing Date
- Jul 8, 2019
- Status
- Granted
- Expiry Date
- Oct 1, 2035
- External Links
- Slate, USPTO, Google Patents