System Of Smart Edge Sensors
Patent No. US11095613 (titled "System Of Smart Edge Sensors") was filed by Nusantao Ip Llc on Mar 27, 2019.
What is this patent about?
’613 is related to the field of securing data in electronic devices, particularly those with multiple sensors that communicate with a central processor. The background involves the increasing vulnerability of sensor data to hacking, especially in devices like cellphones, wearables, and IoT devices. Existing security measures often focus on the communication link and the device's processor/OS, leaving sensor data exposed if these defenses are breached.
The underlying idea behind ’613 is to implement endpoint control by pushing security and encryption to the edge of the network, specifically at the sensor level. Instead of relying solely on securing the processor or communication channels, the invention places a 'smart edge module' directly between the sensor and the device's main processor. This module encrypts the raw sensor data before it ever reaches the processor, ensuring that even if a hacker gains access to the device, they can only access encrypted data.
The claims of ’613 focus on a smart edge module that sits between a sensor and the communication bus of an electronic device. This module includes an interface adapter to receive raw data from the sensor, a bus adapter for communication with the device bus, a module bus connecting these adapters, a module processor for encrypting the raw data, and a module memory storing a module operating system. Some claims specify the inclusion of an encryption accelerator or a command filter to discard unauthorized communications.
In practice, the smart edge module intercepts the raw data signal from the sensor, encrypts it using a key, and then transmits the encrypted signal to the device's processor. The processor only receives encrypted data, so any data stored or transmitted by the processor remains secure. The module can also include a pre-processing stage to filter the raw data, reducing the amount of data that needs to be encrypted and transmitted, thereby saving power and bandwidth. A device driver facilitates communication between the device processor and the smart edge module, handling only encrypted data.
This approach differs from prior solutions by shifting the security focus from the central processor and communication channels to the sensor itself. By encrypting the data at the source, the invention mitigates the risk of data breaches even if other security layers are compromised. The use of a local contract , potentially a blockchain contract, within the smart edge module allows for secure management of encryption keys and access control, ensuring that only authorized parties can decrypt and use the sensor data. The smart edge module can be implemented as a system-on-a-chip (SoC) for enhanced security and integration.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2010s when ’613 was filed, systems commonly relied on processors to handle security measures for data generated by sensors, at a time when security measures were typically targeted at the communication link and the devices themselves. At that time, hardware or software constraints made it non-trivial to implement security and encryption measures directly at the sensor level, pushing security to the edges of the network.
Novelty and Inventive Step
The examiner allowed the application because the closest prior art (Tiell, US Pub. No. 2017/0054611) did not explicitly disclose certain features recited in the independent claims. Specifically, the prior art failed to disclose an encryption accelerator for accelerating encryption of raw data (claim 1), a module processor configured to encrypt raw data according to instructions in a local contract stored in module memory (claim 3), a command filter to discard unauthorized communication directed at the module processor (claim 5), filtering the raw data signal to generate a filtered signal before encryption (claims 11 and 18), a device driver residing in device memory to facilitate communication between the device processor and the security module (claim 12), and maintaining a secure contract in module memory with decryption keys and authorized readers (claim 19). Also, the prior art failed to disclose operating security modules to intercept and decrypt transmissions on the device bus, deciphering headers, and discarding unauthorized transmissions (claim 21). The dependent claims were allowed for the same reasons.
Claims
This patent contains 23 claims, of which claims 1, 6, 8, 11, 12, 18, 19, and 22 are independent. The independent claims generally focus on a smart edge module and an electronic device incorporating such modules, as well as methods for operating these modules to encrypt sensor data. The dependent claims generally elaborate on specific features, configurations, and functionalities of the smart edge module and electronic device described in the independent claims.
Key Claim Terms New
Definitions of key terms used in the patent claims.
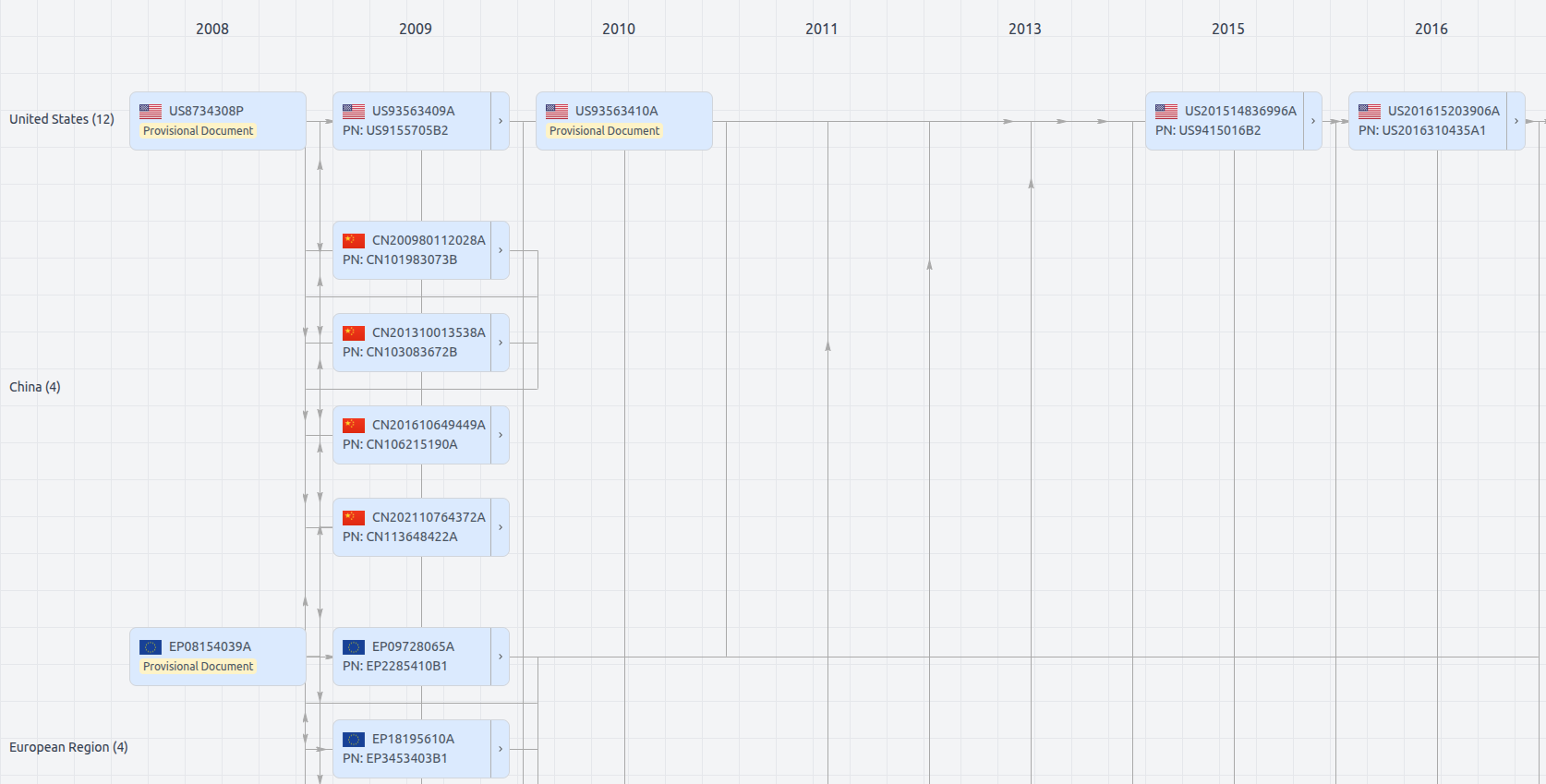
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Get instant alerts for new documents
US11095613
- Application Number
- US16366971
- Filing Date
- Mar 27, 2019
- Status
- Granted
- Expiry Date
- Oct 22, 2039
- External Links
- Slate, USPTO, Google Patents