Secure Zone For Secure Purchases
Patent No. US11201869 (titled "Secure Zone For Secure Purchases") was filed by Fingon Llc on Apr 18, 2019.
What is this patent about?
’869 is related to the field of secure data transactions, particularly those conducted over computer networks. The background acknowledges the vulnerability of online activities like shopping and banking to software-based attacks such as viruses and keyloggers. The patent aims to provide a hardware-based security solution that is resistant to these attacks, creating a more secure environment for sensitive data processing.
The underlying idea behind ’869 is to create a secure zone within a computing device that operates independently of the main operating system. This secure zone is designed to execute sensitive tasks, such as processing credit card information, in an isolated environment. The key insight is to use a dedicated processor and memory within this zone, controlled by a supervisor that enforces strict security policies and validates code before execution.
The claims of ’869 focus on an apparatus and method for executing a task with subtasks within a secure zone. Specifically, the independent claims cover the secure processor's ability to execute a task and its subtasks, store the state of the main task, switch execution to a subtask, clear the subtask's data from memory after execution, and then restore the main task's state to resume its execution.
In practice, the secure zone receives tasks and subtasks, each digitally signed by their respective code providers. The supervisor validates these signatures and applies permissions based on the code provider's digital certificate. This allows for a layered security approach, where different code segments (e.g., merchant code and bank code) have different levels of access and trust. The secure zone can also control peripherals like the screen and keyboard, isolating them from the potentially compromised main operating system.
This approach differs from traditional security measures that rely solely on software. By implementing a hardware-based secure zone, the system can protect sensitive data even if the main operating system is compromised. The use of digitally signed code and permission-based access control further enhances security by ensuring that only trusted code can execute within the secure zone and that it only has access to the resources it needs. The ability to switch between tasks and subtasks, while maintaining a secure and isolated environment, allows for complex secure transactions to be performed with a high degree of confidence.
How does this patent fit in bigger picture?
Technical landscape at the time
In the early 2010s when ’869 was filed, at a time when secure transactions were typically implemented using software-based security measures, systems commonly relied on operating system level security features rather than hardware-based secure zones, and when hardware or software constraints made isolating sensitive data and operations from the main operating system non-trivial.
Novelty and Inventive Step
Claims 1-29 were cancelled. Claims 30-40 were amended. Claims 30-50 were examined and rejected as being unpatentable over prior art. The applicant's arguments were considered but were not persuasive. The rejection was made final. The prosecution record does NOT describe the technical reasoning or specific claim changes that led to allowance.
Claims
This patent contains 23 claims, with independent claims 1 and 12 directed to an apparatus and a method, respectively, both relating to secure processing involving tasks and subtasks within a secure zone. The dependent claims generally elaborate on and refine the features and steps described in the independent claims, providing more specific details about the secure processor's configuration, memory management, and peripheral handling.
Key Claim Terms New
Definitions of key terms used in the patent claims.
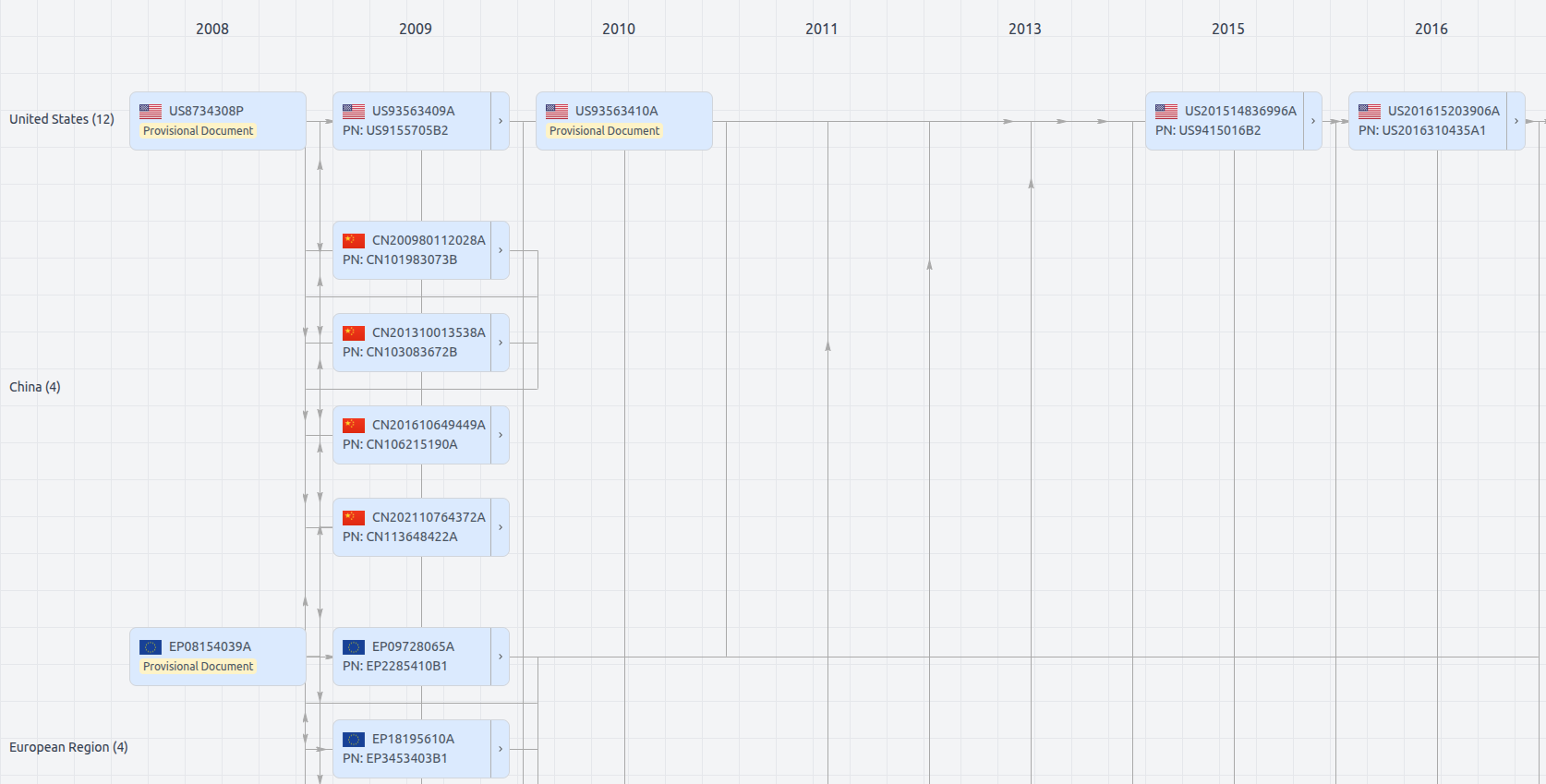
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11201869
- Application Number
- US16388145
- Filing Date
- Apr 18, 2019
- Status
- Granted
- Expiry Date
- Jun 21, 2033
- External Links
- Slate, USPTO, Google Patents