Method For Internet User Authentication
Patent No. US11354667 (titled "Method For Internet User Authentication") was filed by Spriv Llc on Jan 15, 2021.
What is this patent about?
’667 is related to the field of internet user identification and security, specifically addressing the problem of online fraud and identity theft. The background highlights the increasing reliance on internet transactions and the associated risks of transmitting personal and confidential data. Existing methods, such as IP address tracing, have limitations in accurately verifying user identity, creating a need for more robust authentication mechanisms.
The underlying idea behind ’667 is to enhance user authentication by cross-referencing the location of a user's computer with the location of their mobile phone. This is achieved by creating a computer signature based on hardware and software characteristics of the user's computer. The system then compares the geographical location associated with this signature to the current location of the user's mobile phone, providing a more reliable means of verifying the user's identity.
The claims of ’667 focus on a computer system configured to authenticate a user attempting to access the system or conduct a transaction. The system obtains the geographical location of the user's mobile phone and determines if the user's computer signature is associated with a stored geographical location in a database. If a match is found, the system compares the stored location with the phone's current location. If the locations are within an acceptable distance, the user is granted access and/or assigned a positive score. If no match is found initially, the system requests additional authentication information.
In practice, the system first identifies the user's computer signature, which includes software identifiers. Simultaneously, it obtains the user's mobile phone location using methods like GPS or cellular triangulation. The system then checks if this computer signature is already associated with a location in its database. If it is, the system compares the stored location with the phone's current location. This comparison determines whether the user is likely to be who they claim to be, based on the proximity of their computer and phone.
The differentiation from prior approaches lies in the combined use of a computer signature and mobile phone location for authentication. Unlike simple IP address tracing, which can be easily spoofed, this method provides a more reliable verification mechanism. By requiring additional authentication when the computer signature is not recognized or the locations do not match, the system adds an extra layer of security, making it more difficult for fraudsters to gain unauthorized access or conduct fraudulent transactions. The system dynamically learns and updates the association between computer signatures and locations, improving its accuracy over time.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2000s when ’667 was filed, at a time when websites commonly relied on IP addresses to identify users, systems commonly relied on IP addresses to determine the location of the user. At that time, hardware or software constraints made it non-trivial to accurately determine the location of a user's mobile device or computer with high precision.
Novelty and Inventive Step
The examiner allowed the claims because the applicant teaches a computer system for authenticating the identity of users accessing the system to conduct transactions. Each user is associated with a computer signature and is in possession of a mobile phone. The system obtains the geographical location of the mobile phone and determines if the computer signature is associated in a database with a stored geographical location. If the computer signature is associated in the database with the stored geographical location, the system compares the stored geographical location to the geographical location of the mobile phone obtained. If the result of the comparison is a difference in location that is within an acceptable distance, the system allows the user access and/or the ability to conduct transactions and/or assigns to the user a positive score. If the computer signature is not associated in the database with a stored geographical location, then the system attempts to authenticate the identity of the user by other identification information, and only if the identity of the user is authenticated by the identification information, the system stores, in the database, the computer signature in association with the mobile phone geographical location obtained, and carries out at least one of allowing the user access and/or the ability to conduct transactions, assigning to the user a positive score. The computer signature comprises at least one software identifier, and the geographical location of the mobile phone is identified by at least one method selected from the group consisting of Galileo, GPS, cellular antenna network, phone antenna, WiFi, and Bluetooth.
Claims
There are 18 claims in total. Claims 1 and 5 are independent. The independent claims are directed to a computer system configured to authenticate a user's identity using the geographical location of their mobile phone and a computer signature. The dependent claims generally elaborate on the computer signature and detail actions taken based on authentication results.
Key Claim Terms New
Definitions of key terms used in the patent claims.
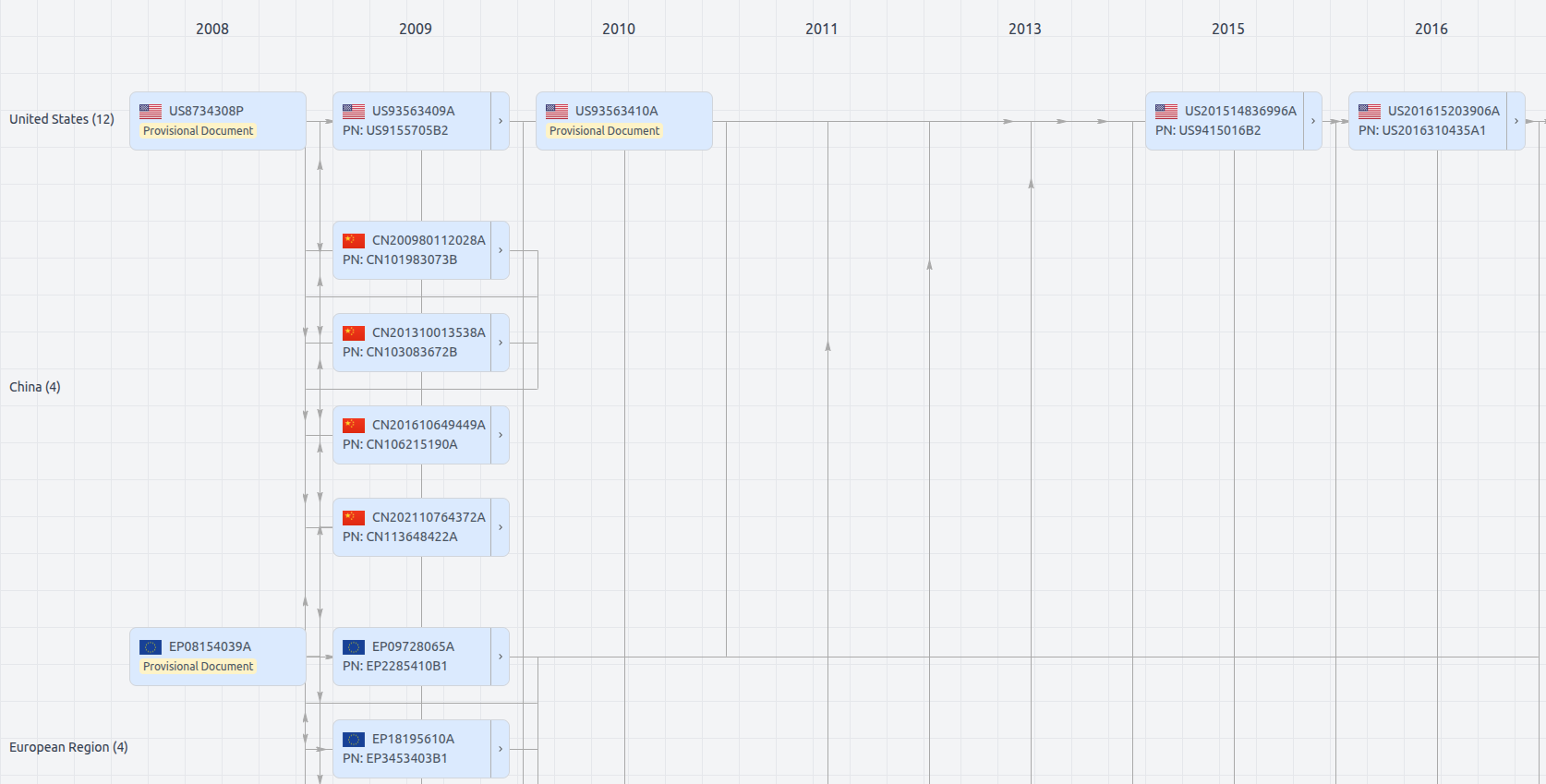
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11354667
- Application Number
- US17149776
- Filing Date
- Jan 15, 2021
- Status
- Granted
- Expiry Date
- May 29, 2027
- External Links
- Slate, USPTO, Google Patents