Smart Edge Co-Processor
Patent No. US11416758 (titled "Smart Edge Co-Processor") was filed by Nusantao Ip Llc on Apr 2, 2020.
What is this patent about?
’758 is related to the field of securing data from sensors in electronic devices, particularly in the context of the Internet of Things (IoT). Traditional sensor architectures provide raw data directly to a device's processor, leaving it vulnerable to hacking. The patent addresses the problem of securing sensor data at the network edge , before it reaches the main processor, to prevent unauthorized access even if the device itself is compromised.
The underlying idea behind ’758 is to interpose a smart edge module between a sensor and the device's main processor. This module intercepts the raw sensor data, encrypts it, and then passes the encrypted data to the processor. This ensures that even if a hacker gains access to the processor or intercepts communications, they will only obtain encrypted data, rendering it useless without the decryption key.
The claims of ’758 focus on a smart edge module comprising a sensor, a hardware co-processor for encrypting the raw signal from the sensor, a secured interface between the sensor and the co-processor, a communication interface for external communication, and an authentication module. Crucially, the authentication module includes a JTAG module for verifying the integrity of the sensor and secured interface, with the co-processor mounted on a PCB board with a JTAG access point.
In practice, the smart edge module operates by receiving raw data from a sensor, pre-processing it to filter out noise or irrelevant information, encrypting the filtered data using a local contract (potentially a blockchain contract) for secure key management, and then transmitting the encrypted data to the device's processor. The JTAG module periodically validates the hardware configuration to detect tampering, ensuring that the sensor and interface haven't been compromised.
This approach differs from prior solutions by pushing security to the sensor level, rather than relying solely on device-level or network-level security measures. By encrypting data at the source, ’758 protects against vulnerabilities in the device's operating system or communication channels. The use of a JTAG dongle for hardware authentication adds an additional layer of security, preventing physical tampering and ensuring the integrity of the entire system from sensor to processor.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2010s when ’758 was filed, security measures were typically targeted at the communication link and the devices themselves. At a time when security and privacy were implemented on top of processors with millions of gates and operating systems with millions of lines of code, the attack surface area was dramatically increasing due to the Internet of Things (IoT) and artificial intelligence (AI) applications.
Novelty and Inventive Step
The examiner approved the application because the prior art does not teach or suggest the specific claim limitations recited in independent claims 1 and 18, taken as a whole. Specifically, the examiner stated that Chou, Varadarajan, and Chen disclose a smart module, sensor sensing physical events, generating an encrypted signal, a secured interface, and a communication interface handling communications, but do not teach or suggest the specific combination of elements as claimed.
Claims
This patent contains 10 claims, with independent claims 1 and 9. Independent claim 1 is directed to a smart edge module configured to sense physical events and output a corresponding electronic signal, while independent claim 9 is directed to a smart edge module configured to receive an electronic signal and generate corresponding physical events. The dependent claims generally elaborate on specific features, components, or configurations of the smart edge module described in the independent claims.
Key Claim Terms New
Definitions of key terms used in the patent claims.
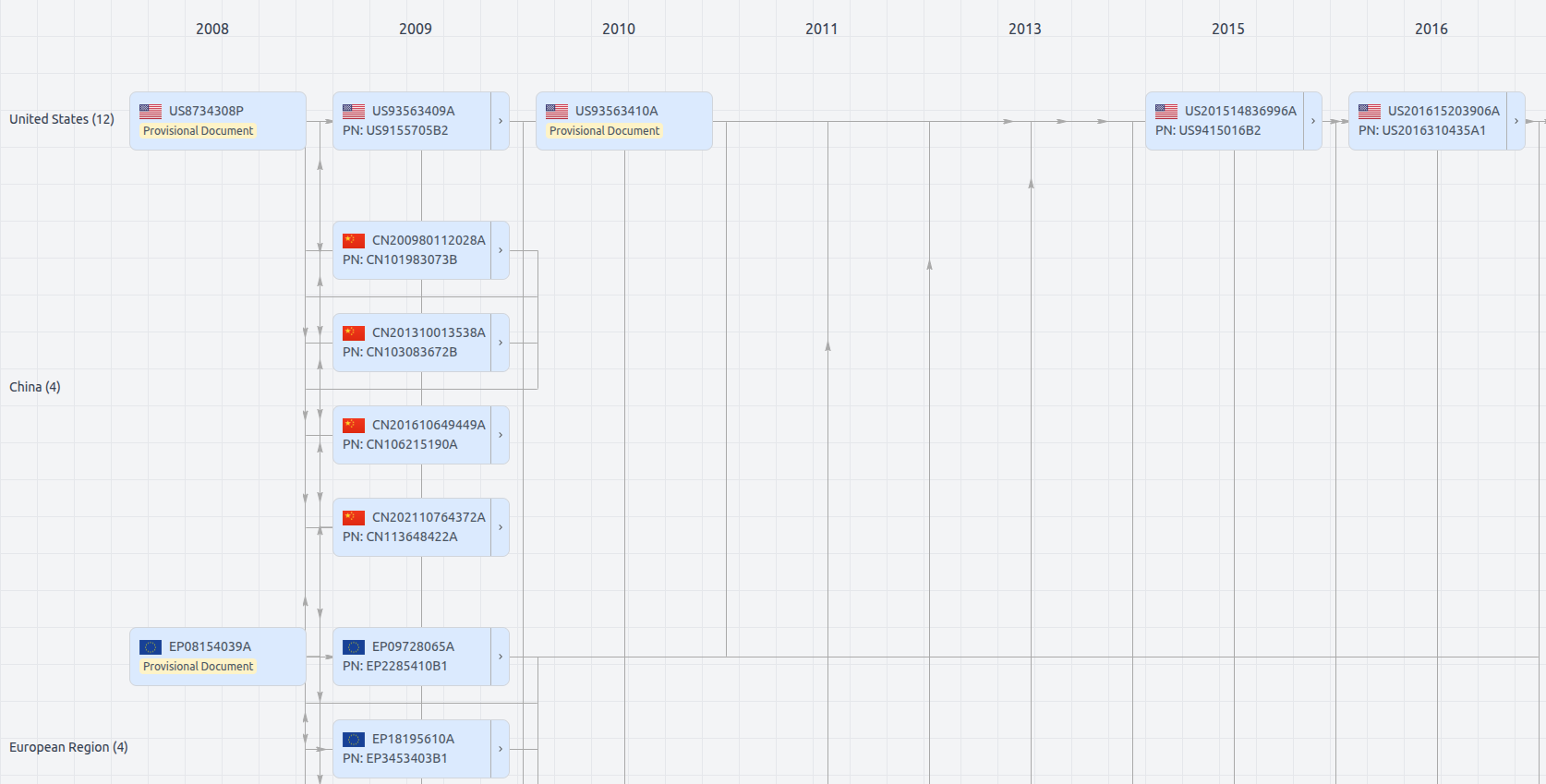
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11416758
- Application Number
- US16838676
- Filing Date
- Apr 2, 2020
- Status
- Granted
- Expiry Date
- Feb 9, 2041
- External Links
- Slate, USPTO, Google Patents