System For User Authentication
Patent No. US11556932 (titled "System For User Authentication") was filed by Spriv Llc on Jun 7, 2022.
What is this patent about?
’932 is related to the field of internet security and user authentication. The background involves the increasing need to verify user identities during online transactions to combat fraud and identity theft. Traditional methods rely on IP addresses, which can be easily spoofed or may not provide sufficient accuracy. The patent addresses the problem of reliably authenticating users accessing websites or conducting transactions online.
The underlying idea behind ’932 is to enhance user authentication by cross-referencing the location of a user's computer with the location of their cell phone. The system leverages the fact that a user's computer and cell phone are likely to be in close proximity during a legitimate transaction. By comparing the geographical locations obtained from these two devices, the system can increase the confidence in the user's identity.
The claims of ’932 focus on a computer system that receives a computer signature (a unique identifier derived from hardware and software characteristics) and the geographical location of the user's cell phone. The system checks if the computer signature exists in a database. If it does, the system compares the current cell phone location with a previously stored location associated with that signature. If the signature is not in the database, the system requests additional authentication information.
In practice, the system first identifies the user's computer signature and obtains the cell phone's location using technologies like GPS or Wi-Fi triangulation. If the computer signature is new, the system prompts the user for additional verification, such as a one-time password. Upon successful authentication, the computer signature and cell phone location are stored in the database. Subsequent access attempts are then validated by comparing the current and stored cell phone locations, allowing or denying access based on the proximity of these locations.
This approach differentiates itself from prior solutions by combining device-specific information (computer signature) with location data from a separate device (cell phone). Unlike IP address-based methods, this system is more resistant to spoofing because it requires physical co-location. The use of a database to store previously authenticated locations allows the system to learn and adapt to a user's typical behavior, reducing the need for repeated authentication while maintaining a high level of security .
How does this patent fit in bigger picture?
Technical landscape at the time
In the mid-2000s when ’932 was filed, systems commonly relied on IP addresses to identify users accessing websites. At a time when hardware or software constraints made precise geolocation non-trivial, determining the geographical location of an internet user's computer and comparing it to the location of their communication device presented technical challenges. Furthermore, authenticating users often involved static credentials, and dynamically cross-referencing multiple sources of location data to verify identity was not a widely adopted practice.
Novelty and Inventive Step
The examiner approved the application because it teaches a computer system for authenticating users accessing the system to conduct transactions. The system associates each user with a computer signature and requires them to possess a mobile phone. The system obtains the geographical location of the mobile phone, determines if the computer signature is associated with a stored geographical location in a database, and compares the stored location to the phone's location. If the locations are within an acceptable distance, the user is granted access. If the computer signature is not associated with a stored location, additional authentication is required. Only if the additional identity is authenticated is the computer signature stored in the database with the mobile phone's location. The system then allows user access and/or the ability to conduct transactions, assigning to the user a positive score, wherein the computer signature comprises at least one software identifier. The examiner stated that these limitations, in conjunction with other limitations in the claims, were not shown by, nor would have been obvious over the prior art.
Claims
This patent contains 20 claims, with claim 1 being the only independent claim. The independent claim focuses on a computer system configured to authenticate a user's identity using cell phone location and computer signature when accessing a website or conducting a transaction. The dependent claims generally elaborate on and refine the specifics of the computer system, the computer signature, the authentication process, and the location determination methods described in the independent claim.
Key Claim Terms New
Definitions of key terms used in the patent claims.
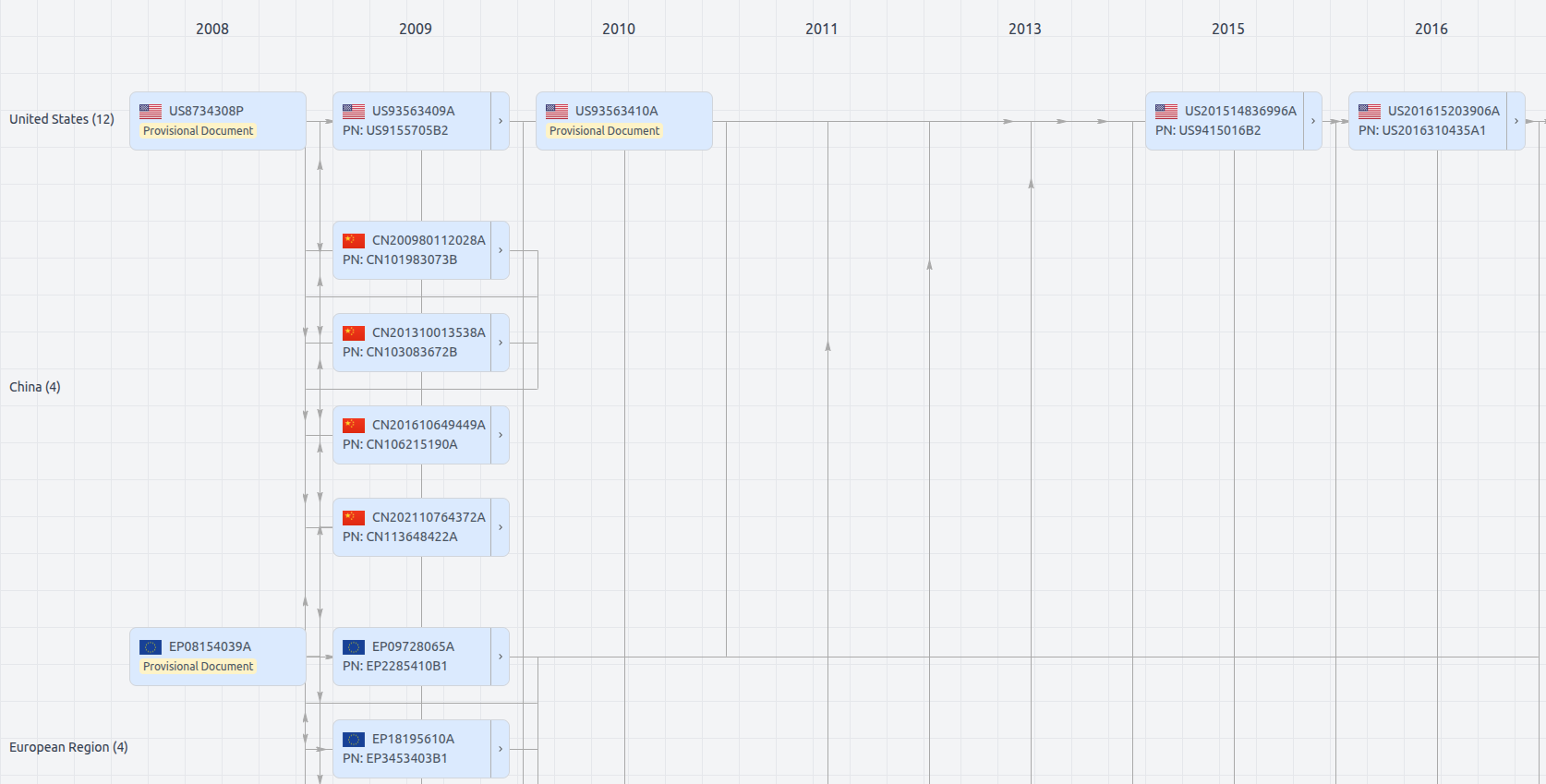
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Get instant alerts for new documents
US11556932
- Application Number
- US17834769
- Filing Date
- Jun 7, 2022
- Status
- Granted
- Expiry Date
- May 29, 2027
- External Links
- Slate, USPTO, Google Patents