Private Data Sharing System
Patent No. US11637802 (titled "Private Data Sharing System") was filed by Brian Moffat Private Data Llc on Sep 23, 2021.
What is this patent about?
’802 is related to the field of secure data sharing systems , particularly those designed to protect user privacy in online social networks and other data sharing platforms. Traditional data sharing systems often allow the hosting service to access and exploit user data, raising privacy concerns. The patent addresses the need for a system where users have greater control over who can access their information.
The underlying idea behind ’802 is to ensure that user data is stored and transmitted in an encrypted form such that only the user and their designated contacts can decrypt and view it. This is achieved by having the encryption and decryption keys reside solely with the users and their contacts, preventing the hosting service from accessing the unencrypted data. The system facilitates the secure exchange of decryption keys between users, ensuring that only authorized parties can access the information.
The claims of ’802 focus on a method for data exchange involving a third-party server and multiple personal computing devices. The method involves creating an original data file, generating encryption and decryption keys, encrypting the data file, encrypting the decryption key separately for each recipient using their unique encryption keys, transmitting all encrypted components to the third-party server, and then forwarding the appropriate encrypted components to each recipient. The key aspect is that the third-party server never has access to the original data file or the decryption key .
In practice, the invention allows a user to create a document, photo, or video and share it with specific individuals without the risk of the hosting service or unauthorized parties accessing the content. The user's device encrypts the data and the decryption key is separately encrypted for each recipient. This ensures that even if the third-party server is compromised, the data remains secure because the server lacks the necessary keys to decrypt it. The recipients then use their own private keys to unlock the decryption key and access the original data.
This approach differs significantly from prior solutions where the hosting service often holds the decryption keys or has the ability to access user data. By distributing the decryption keys solely to the intended recipients, ’802 provides a higher level of privacy and security . This makes it more difficult for the hosting service to exploit user data or for hackers to gain unauthorized access, as they would need to compromise each individual user's device to obtain the necessary decryption keys.
How does this patent fit in bigger picture?
Technical landscape at the time
In the early 2010s when ’802 was filed, at a time when online social networks were becoming increasingly popular, systems commonly relied on centralized servers for data storage and transmission. At a time when X was typically implemented using Y, security and privacy concerns were growing, and hardware or software constraints made B non-trivial, especially regarding user control over data encryption and decryption.
Novelty and Inventive Step
The examiner approved the application because the allowable claims (156-161) are patentable over the prior art. The prior art of record fails to teach or render obvious the limitations recited in each of independent claim 156 and its associated dependent claims.
Claims
This patent contains 6 claims, with claim 1 being independent. Independent claim 1 is directed to a method for data exchange between personal computing devices using a third-party server for storage and transmission, with encryption and decryption modules on each device. The dependent claims elaborate on aspects of the method described in claim 1, such as key generation and disabling decryption keys.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
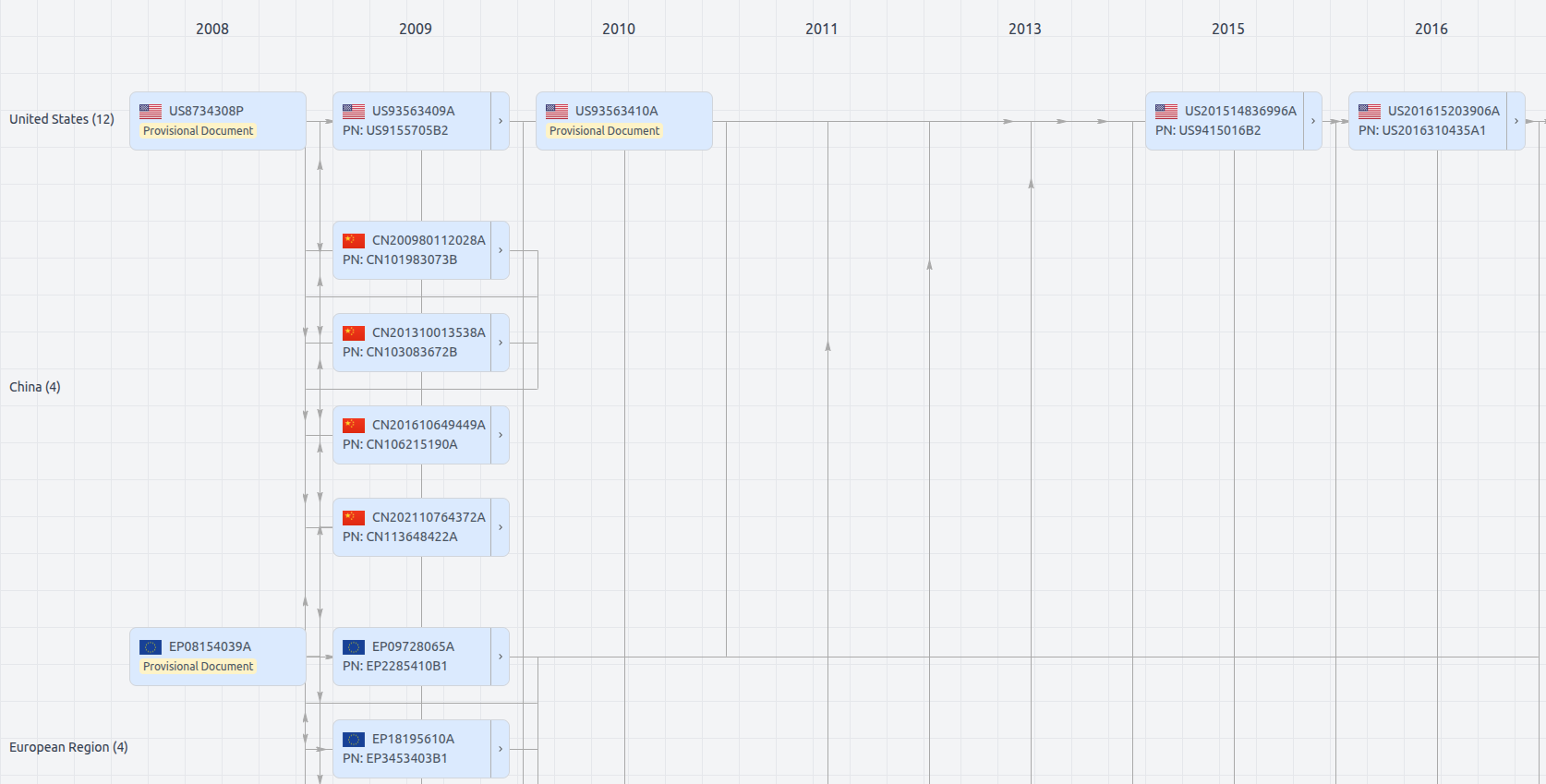
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11637802
- Application Number
- US17483683
- Filing Date
- Sep 23, 2021
- Status
- Granted
- Expiry Date
- Oct 7, 2031
- External Links
- Slate, USPTO, Google Patents