Managing Access To Data And Managing Operations Performed By Applications
Patent No. US11640546 (titled "Managing Access To Data And Managing Operations Performed By Applications") was filed by Nusantao Ip Llc on Apr 2, 2020.
What is this patent about?
’546 is related to the field of data security and access management, particularly concerning the use of sensitive data by applications such as artificial intelligence models. The background involves an increasing concern over the misuse of personal data collected by various devices and sensors, as AI becomes more sophisticated and capable of extracting unintended inferences. Current systems primarily focus on user authentication, leaving application instances and AI models largely unverified, leading to potential privacy breaches and data exploitation.
The underlying idea behind ’546 is to introduce a system architecture that controls access to data and manages the operations that applications are allowed to perform, based on the identity and authentication of those applications. This is achieved through a secure edge module that acts as a trusted environment, managing access to data sets and authenticating applications before allowing them to operate on the data. The system uses smart contracts to define the permissions and restrictions for each application, ensuring that data is used only for its intended purpose.
The claims of ’546 focus on a method and apparatus for managing data access and application operations. Specifically, the independent claims cover obtaining a smart contract associated with a data set, a secure edge module, and an AI model; determining if the AI model is allowed to generate inferences based on the smart contract; executing the AI model to generate inferences if permitted; and performing post-processing operations based on the smart contract. The claims also emphasize that the smart contract dictates permissions for the data, the AI model, and the generated inferences, as well as identifying stakeholders.
In practice, the invention involves a secure edge module that programmatically enforces the rules defined in the smart contract. When an application requests access to data, the secure edge module verifies the application's identity (e.g., by checking a hash or serial number) against the smart contract. If authorized, the application is allowed to execute within the secure edge module, using data that is decrypted only within this secure environment. Post-processing operations, such as deleting the data or encrypting the output, are also dictated by the smart contract, ensuring data security and compliance.
This approach differs significantly from prior solutions by shifting the focus from user authentication to application authentication and authorization. Instead of simply granting access based on user credentials, ’546 ensures that each application instance is verified and limited to specific operations, preventing unauthorized data usage. The use of smart contracts provides a flexible and auditable mechanism for managing data access, while the secure edge module creates a trusted environment that protects sensitive data from unauthorized access and misuse, even if other parts of the system are compromised. The blockchain provides an immutable record of changes to the smart contracts.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2010s when ’546 was filed, data privacy concerns were growing at a time when machine learning models were increasingly being used to analyze personal data. At that time, systems commonly relied on centralized data processing, and securing data at the network edge was non-trivial due to hardware and software constraints.
Novelty and Inventive Step
The examiner approved the application because prior art references, while related to the general field of the invention, did not teach the specific claimed invention. Specifically, the prior art did not disclose the combination of transforming an AI model to perform inference on encrypted data, generating parameter information for encrypting data based on the transformed AI model, transmitting this parameter information to an external device, receiving encrypted data, and outputting an inference result. Furthermore, the prior art did not teach receiving an indication of an AI inferencing event, computing a hash of a machine learning model, sending a record with the hash to a verification system, receiving verification that the hash matches another model, storing the record in a distributed ledger, and providing the AI result to a user upon receiving verification. Finally, the prior art did not teach initiating and performing contextualized AI inferencing with a gateway computing device.
Claims
This patent contains 22 claims, with independent claims numbered 1, 11, 15, 17, 18, 19, and 20. The independent claims generally focus on methods, apparatus, and storage mediums for controlling the execution of artificial intelligence models on data using smart contracts and secure edge modules. The dependent claims generally elaborate on and add limitations to the independent claims.
Key Claim Terms New
Definitions of key terms used in the patent claims.
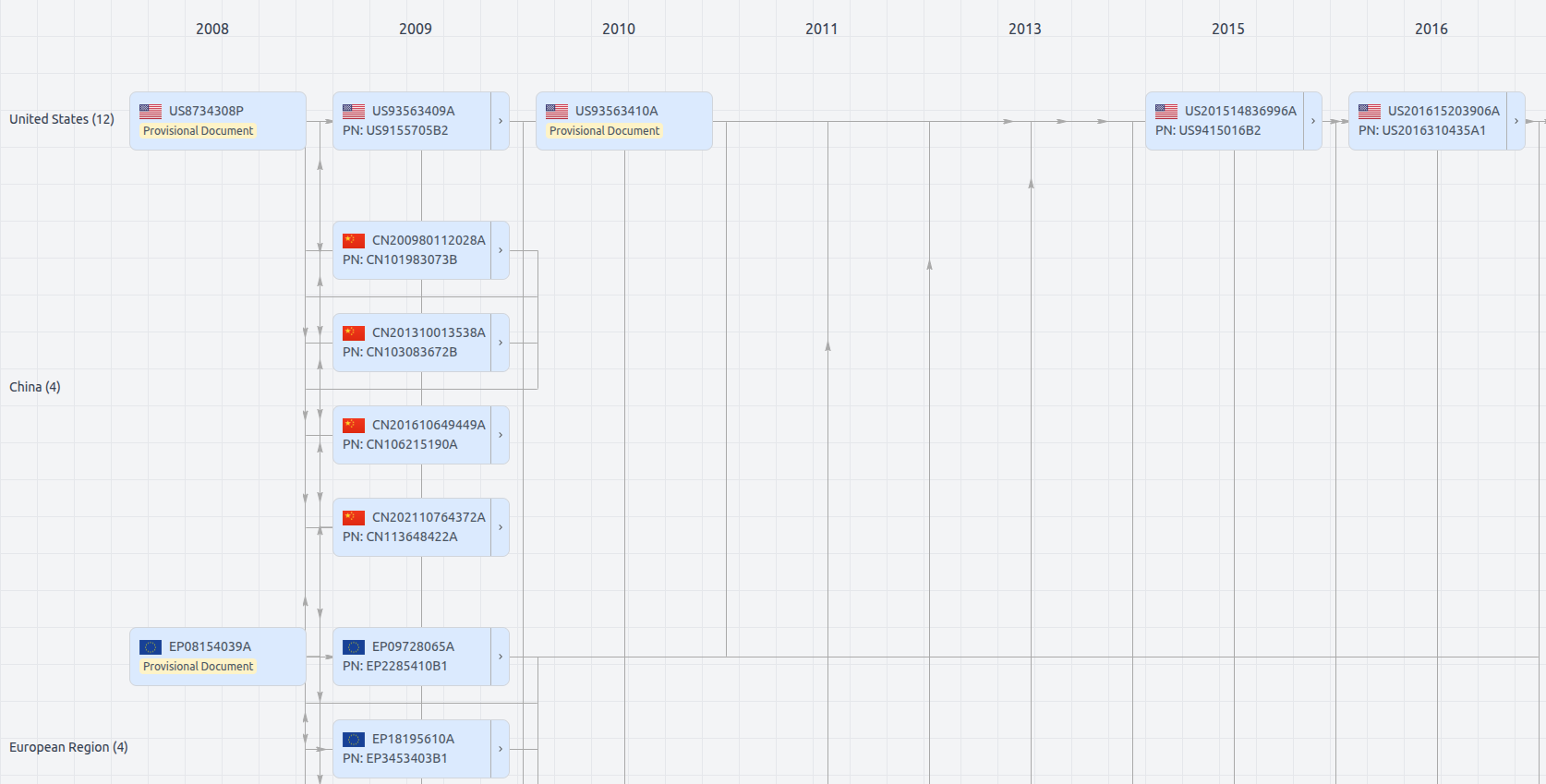
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11640546
- Application Number
- US16839005
- Filing Date
- Apr 2, 2020
- Status
- Granted
- Expiry Date
- Apr 18, 2041
- External Links
- Slate, USPTO, Google Patents