Wireless Base Station And Wireless Communication Terminal And Wireless Communication System
Patent No. US11672028 (titled "Wireless Base Station And Wireless Communication Terminal And Wireless Communication System") was filed by Sovereign Peak Ventures Llc on Feb 10, 2020.
What is this patent about?
’028 is related to the field of wireless communication systems, particularly those operating in spot communication areas like Wi-Fi hotspots. The background involves the increasing use of wireless LAN in portable devices and the need to quickly establish connections in areas where a device might only be in range for a short period. Traditional wireless LAN connections require authentication, which can take time, hindering rapid data transfer in these scenarios.
The underlying idea behind ’028 is to expedite the connection process between a mobile device and a base station by using a two-tiered connection approach . The initial connection is unauthenticated, allowing for quick access to a limited set of data, such as metadata or cached content. This is followed by a standard, authenticated connection for full access, leveraging the initial connection to speed up the setup of the second.
The claims of ’028 focus on a wireless communication device with wireless communication circuitry and control circuitry . The device establishes a connection with a wireless station using both a non-authenticated and an authenticated component. Crucially, during the initial non-authenticated phase, the device receives information necessary for setting up the subsequent authenticated connection, such as channel information. The device then receives content during the authenticated phase, and additional related information during the non-authenticated phase.
In practice, a mobile device entering a Wi-Fi hotspot would first establish a quick, unauthenticated connection with the base station. During this phase, the base station would transmit the necessary parameters for a secure, authenticated connection, such as the correct channel and encryption keys. This pre-configuration allows the device to bypass the time-consuming channel scanning and authentication steps, leading to a faster secure connection and quicker access to the desired content.
This approach differentiates itself from prior solutions by splitting the connection process into two distinct phases. Instead of performing all authentication steps upfront, ’028 prioritizes speed by initially providing limited access without authentication, using this initial connection to prepare for a more secure and complete connection. This is particularly useful in scenarios where the mobile device is moving rapidly through the communication area, maximizing the amount of data that can be transferred during the limited time available.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2000s when ’028 was filed, wireless communication systems commonly relied on established protocols for authentication and connection establishment between base stations and terminals. At a time when wireless LAN technologies were becoming increasingly prevalent in portable devices, reducing the connection time and improving the efficiency of data transfer in spot communication areas were significant technical challenges. When hardware or software constraints made fast handovers and seamless connectivity non-trivial, especially for mobile devices moving at high speeds through these areas.
Novelty and Inventive Step
The examiner approved the application because the prior art references, taken individually or in combination, did not anticipate, disclose, teach, or suggest the specific claim combinations. Specifically, while one reference disclosed partially opening a controlled port for non-authenticated requests, and other references disclosed configuration information for establishing communication and authentication methods, none of them suggested the claimed combination of controlling wireless communication circuitry to receive content during both authenticated and non-authenticated components of a connection, along with using communication channel information for selecting a communication channel during the authenticated component.
Claims
This patent includes 14 claims, with independent claims 1 and 12 directed to a wireless communication device configured to communicate with a wireless station using both non-authenticated and authenticated connection components. The dependent claims generally elaborate on the type of information exchanged during the non-authenticated component, including profile information, metadata, and identification information, as well as implementation details of the wireless communication circuitry and control circuitry.
Key Claim Terms New
Definitions of key terms used in the patent claims.
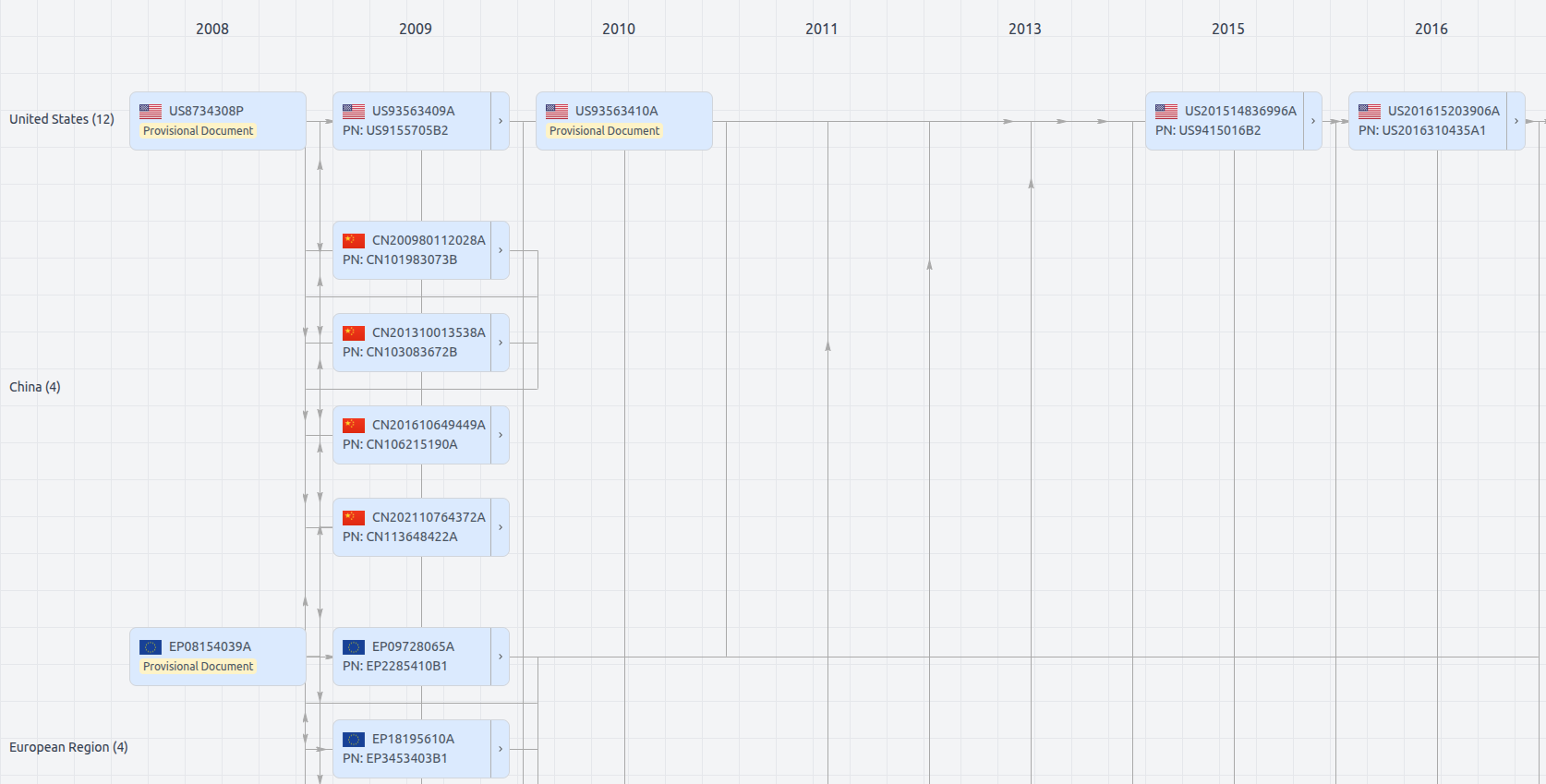
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11672028
- Application Number
- US16786582
- Filing Date
- Feb 10, 2020
- Status
- Granted
- Expiry Date
- Jan 3, 2031
- External Links
- Slate, USPTO, Google Patents