Systems And Methods For Detecting Injection Exploits
Patent No. US11736499 (titled "Systems And Methods For Detecting Injection Exploits") was filed by Corner Venture Partners Llc on Apr 9, 2020.
What is this patent about?
’499 is related to the field of computer security, specifically the detection of injection exploits in networked computing environments. Web applications are vulnerable to attacks where malicious code is injected into commands or queries, leading to unauthorized access or system compromise. Traditional security measures often struggle to identify these exploits effectively, especially zero-day attacks or those employing sophisticated evasion techniques. The patent addresses the need for a more robust and dynamic approach to detect and respond to injection exploits in real-time.
The underlying idea behind ’499 is to dynamically model the expected behavior of a web application after an execution function (a function accepting external data) is invoked. By comparing the actual runtime behavior to this model, deviations indicative of malicious code injection can be identified. This involves constructing a representation of the legitimate execution flow, such as an abstract syntax tree (AST) , program dependency graph, or SQL parse tree, and then monitoring for anomalies that suggest an injection attack is underway. The key insight is that injection attacks alter the expected execution path, leaving detectable traces in the application's behavior.
The claims of ’499 focus on a method implemented by a collector server for detecting injection exploits. The method involves monitoring executing web applications, detecting the invocation of execution functions that accept external data, generating a model of legitimate behavior following the invocation, comparing actual behavior to the model, and generating an alert when deviations occur. Crucially, the claims require validation that the deviation is due to functions accepting external input , linking the anomalous behavior back to a potential injection point.
In practice, the invention uses application-level hooks to trace data flow from external inputs (like GET/POST requests) to execution functions. For example, in SQL injection detection, the system constructs a parse tree of the SQL query and compares it to a baseline. If an attacker injects malicious SQL, the parse tree will be altered, triggering an alert. Similarly, for OS command injection, the system monitors for unexpected child processes spawned by execution functions. This dynamic analysis allows the system to detect a wide range of injection attacks, including SQL, NoSQL, OS command, and LDAP injection.
The invention differentiates itself from prior approaches by focusing on dynamic behavioral analysis rather than static signature matching. Traditional web application firewalls (WAFs) rely on predefined patterns, which can be bypassed by sophisticated attackers. By modeling legitimate behavior and detecting deviations, ’499 can identify novel attacks and those employing evasion techniques. Furthermore, the system can pinpoint the vulnerable code path, aiding in remediation. The use of program dependency graphs and abstract syntax trees provides a detailed view of application execution, enabling more accurate and reliable exploit detection.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2010s when ’499 was filed, web applications were commonly implemented using a variety of languages such as PHP, JAVA, and Python, at a time when systems typically relied on API calls and methods accepting user input (e.g., GET, POST) to handle data. It was also a time when hardware or software constraints made real-time, deep packet inspection non-trivial for large enterprises, and systems commonly relied on application execution monitoring to trace code execution and platform monitoring for installations and processes.
Novelty and Inventive Step
The examiner approved the application because the prior art of record, whether considered individually or in combination, does not teach or fairly suggest using a collector server to monitor web applications, detect when an execution function is received and invoked (where the function accepts external free-form data values), detect malicious code by generating a model of legitimate behavior after the function is invoked, compare actual behavior to the model, generate an alert when behavior deviates, and validate whether the deviation is due to functions accepting external input.
Claims
This patent contains 15 claims, with claim 1 being the only independent claim. Independent claim 1 is directed to a method for detecting injection exploits in a networked computing environment by monitoring web applications, detecting execution functions, generating a model of legitimate behavior, comparing actual behavior to the model, and generating an alert when deviations occur. The dependent claims generally elaborate on the type of execution function, the method of generating a model of legitimate behavior, the method of comparing actual behavior to the model, and remediation actions.
Key Claim Terms New
Definitions of key terms used in the patent claims.
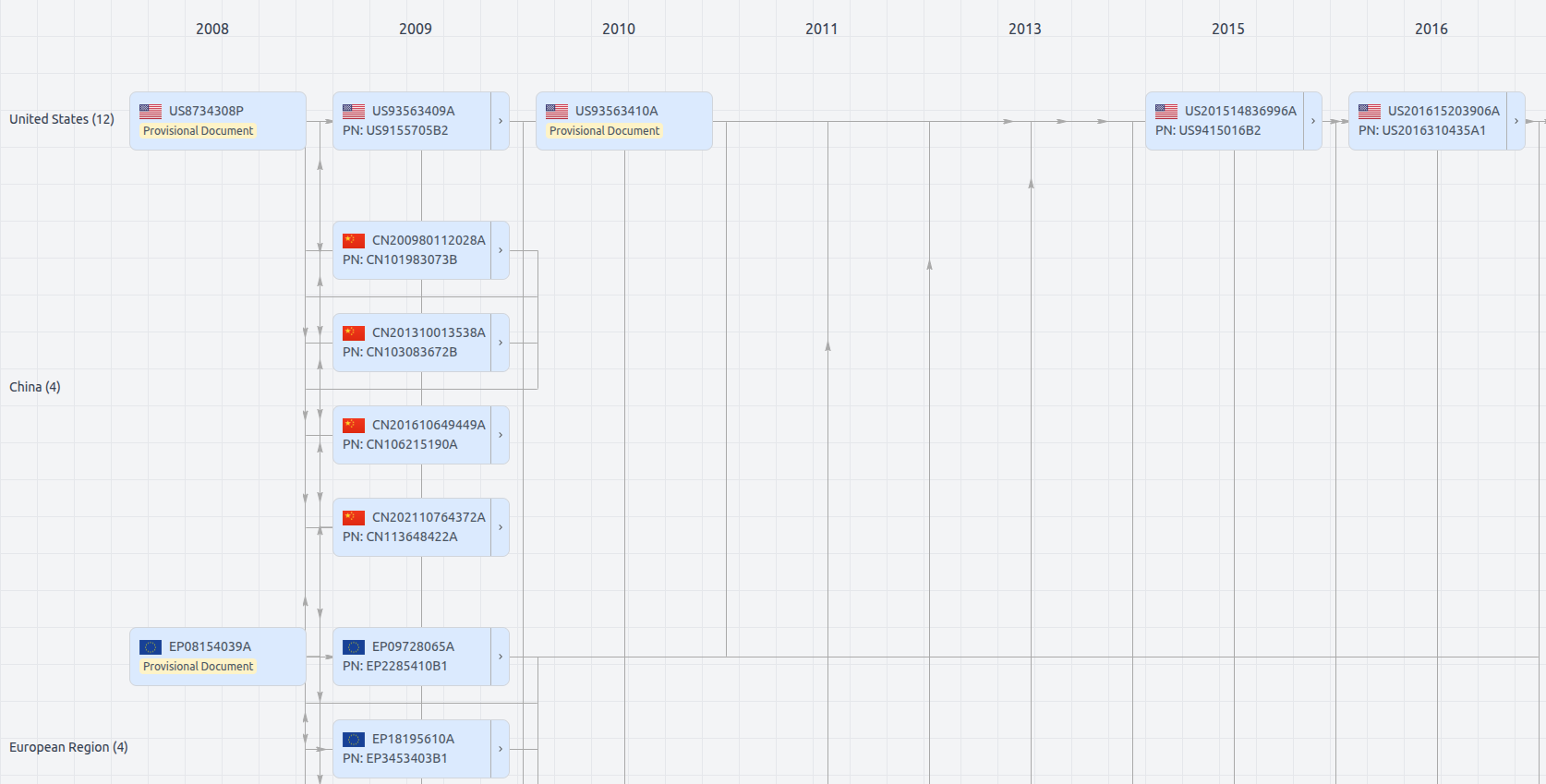
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11736499
- Application Number
- US16844915
- Filing Date
- Apr 9, 2020
- Status
- Granted
- Expiry Date
- Jan 26, 2041
- External Links
- Slate, USPTO, Google Patents