Embedded Universal Integrated Circuit Card Supporting Two-Factor Authentication
Patent No. US11916893 (titled "Embedded Universal Integrated Circuit Card Supporting Two-Factor Authentication") was filed by Network-1 Technologies Inc on Dec 10, 2021.
What is this patent about?
’893 is related to the field of wireless communication , specifically addressing the challenges of managing network access credentials in embedded universal integrated circuit cards (eUICCs). Traditional SIM cards are difficult to manage in machine-to-machine (M2M) applications due to remote locations and the need for hermetically sealed devices. eUICCs offer a software-based solution, but securely transferring network credentials remains a challenge, especially while maintaining compatibility with existing networks that rely on pre-shared secret keys.
The underlying idea behind ’893 is to enhance the security and flexibility of eUICCs by implementing a two-factor authentication scheme and a mechanism for mutually deriving a network key . The mobile device initially connects to the network using a first set of credentials, then authenticates the user or device using a second factor. After successful second-factor authentication, a symmetric key is provided, enabling the decryption of a second set of network credentials. This allows the mobile network operator (MNO) to retain control over the use of the second key, even if the eUICC profile is distributed outside of the MNO's direct control.
The claims of ’893 focus on a mobile device with an eUICC that is configured to communicate with a wireless network. The device includes a memory for storing the eUICC identity, a random number generator for creating an eUICC private key, and a radio for transmitting the eUICC identity and public key to a subscription manager. The eUICC itself is configured to derive a profile key using an elliptic curve Diffie-Hellman (ECDH) key exchange, decrypt portions of the eUICC profile using both the profile key and a symmetric key, and generate a response value for authenticating with the wireless network using a key K.
In practice, the invention allows a mobile device to connect to a wireless network using a first set of credentials, which might provide limited access. The user then authenticates using a second factor, such as entering credentials on a web page. Upon successful authentication, the MNO provides a symmetric key that unlocks the second set of network credentials, enabling full network access. This approach differs from prior solutions by adding a layer of security and control for the MNO, as the second set of credentials remains encrypted until the user is properly authenticated.
This approach also allows for the dynamic rotation of network keys without requiring physical intervention or the distribution of new eUICC profiles. The MNO and the mobile device can mutually derive a new key using a key derivation algorithm and a shared token. This enables the mobile device to disconnect from the network and reconnect using the newly derived key, enhancing security and reducing the costs associated with managing network access credentials.
How does this patent fit in bigger picture?
Technical landscape at the time
In the early 2010s when ’893 was filed, machine-to-machine (M2M) communication was an emerging field, at a time when wireless wide area networks were typically designed and optimized for mobile phones. Systems commonly relied on subscriber identity module (SIM) cards within 2G networks and a related universal integrated circuit card (UICC) for 3G and 4G networks, including LTE networks. The use of wireless technologies with M2M communications created new opportunities for the deployment of M2M modules in locations less suitable for fixed-wire Internet access, but hardware or software constraints made securely and electronically transferring a new set of MNO network access credentials (such as an IMSI and network key K) to a module in a secure and efficient manner non-trivial.
Novelty and Inventive Step
The examiner allowed the claims because the prior art, whether taken individually or in combination, failed to disclose or make obvious the following: receiving an eUICC profile from a subscription manager that includes network parameters, a key K, a subscriber identity, and a symmetric key; decrypting a first portion of the eUICC profile using a profile key; and decrypting a second portion of the eUICC profile using the symmetric key, where the second portion includes the key K and the subscriber identity.
Claims
This patent contains 17 claims, with claim 1 being the only independent claim. Independent claim 1 is directed to a mobile device configured for wireless network communication, focusing on the device's components and their interactions for secure profile management using an embedded universal integrated circuit card (eUICC). The dependent claims elaborate on and further define the elements and functionalities described in the independent claim, providing more specific details and alternative embodiments of the mobile device and its components.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
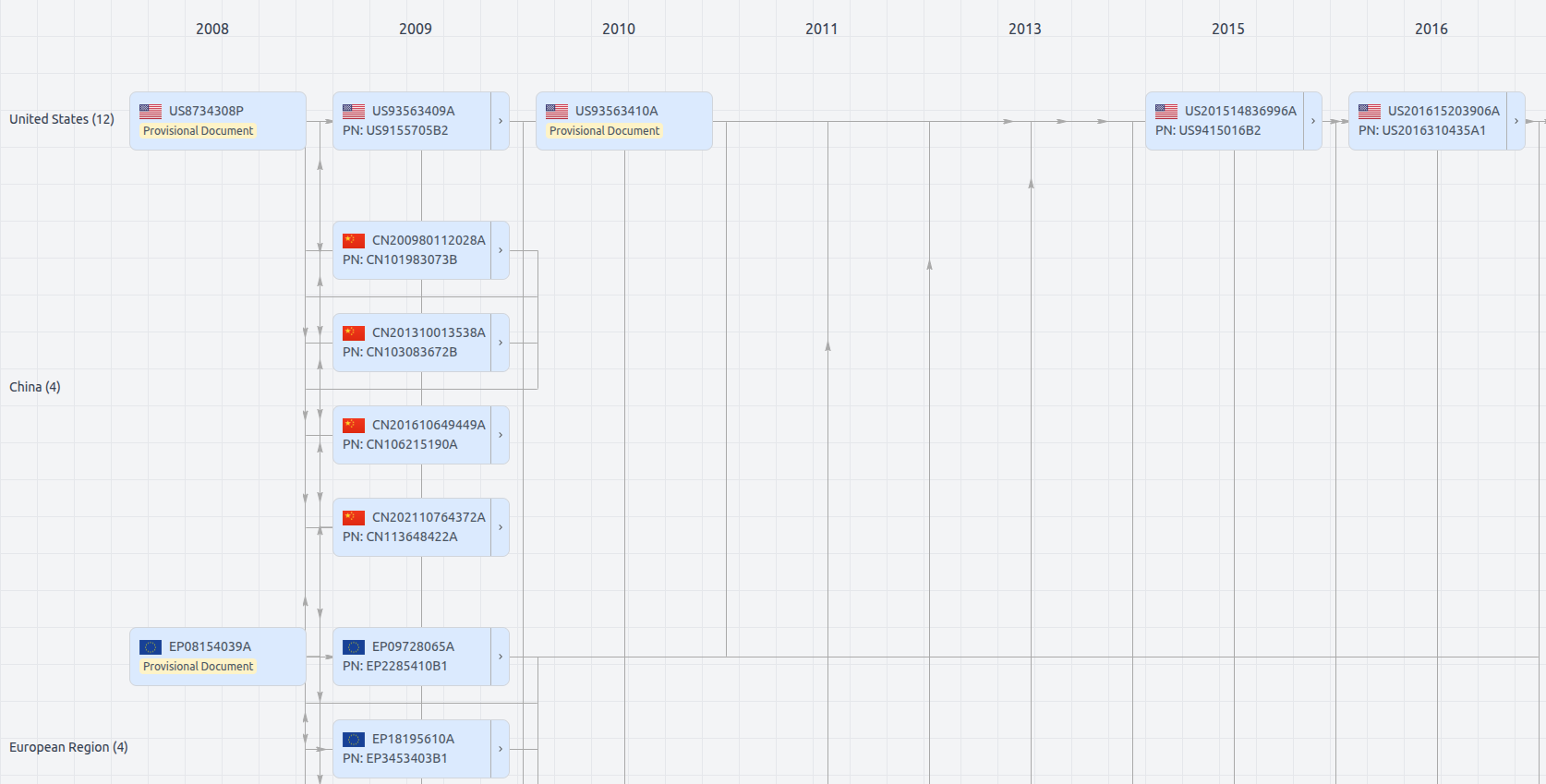
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Get instant alerts for new documents
US11916893
- Application Number
- US17547990
- Filing Date
- Dec 10, 2021
- Status
- Granted
- Expiry Date
- Dec 6, 2033
- External Links
- Slate, USPTO, Google Patents