Systems And Methods For “Machine-To-Machine” (M2M) Communications Between Modules, Servers, And An Application Using Public Key Infrastructure (Pki)
Patent No. US11973864 (titled "Systems And Methods For “Machine-To-Machine” (M2M) Communications Between Modules, Servers, And An Application Using Public Key Infrastructure (Pki)") was filed by Network-1 Technologies Inc on Feb 20, 2023.
What is this patent about?
’864 is related to the field of secure communication between devices, specifically focusing on Machine-to-Machine (M2M) communication and the Internet of Things (IoT). The background involves the increasing use of low-cost sensors and internet connections for remote monitoring, which raises concerns about security, battery life, and efficient use of radio spectrum. Existing security protocols like IPSec, TLS, and SSL are often too resource-intensive for these applications, especially when devices sleep for extended periods.
The underlying idea behind ’864 is to establish a secure and efficient communication channel between a module (e.g., a sensor device) and a server using public key infrastructure (PKI) , but without the overhead of traditional security protocols. The module derives its own private/public key pair using cryptographic algorithms. A pre-shared secret key is used initially to authenticate the module to the server. Subsequently, a symmetric ciphering key is derived using an elliptic curve integrated encryption scheme (ECIES) to enable efficient and secure data transfer.
The claims of ’864 focus on a method comprising storing a server public key, a module identity, cryptographic algorithms, and a pre-shared secret key; deriving a module private key and a corresponding module public key; deriving a symmetric ciphering key using an elliptic curve integrated encryption scheme (ECIES) ; generating module encrypted data using the symmetric ciphering key and the symmetric ciphering algorithm, wherein the module encrypted data includes the module identity; sending a message to a server for a wireless network, the message comprising the module encrypted data and the corresponding module public key, wherein the server mutually derives the symmetric ciphering key using at least the module public key; and authenticating the mobile device with the wireless network using a message digest with the pre-shared secret key.
In practice, the module first authenticates itself to the server using a pre-shared secret key. This initial authentication allows the server to securely receive the module's derived public key. The server then uses this public key, along with its own private key and ECIES, to derive a symmetric key that is shared with the module. All subsequent communication between the module and the server is encrypted using this symmetric key, which is computationally less expensive than asymmetric encryption, saving battery power and bandwidth.
This approach differs from prior solutions by avoiding the need for complex handshakes and key exchanges at the network and transport layers. The use of a pre-shared secret key for initial authentication provides a secure way to establish trust, while the subsequent use of a derived symmetric key ensures efficient and secure communication for small, periodic messages. The key derivation function and the use of symmetric encryption after initial authentication are key differentiators, enabling secure and efficient M2M communication.
How does this patent fit in bigger picture?
Technical landscape at the time
In the early 2010s when ’864 was filed, machine-to-machine (M2M) communication was an emerging field, at a time when wireless technologies like WiFi, 3G, and 4G LTE were becoming more prevalent. Securing these communications was a concern, but established security protocols like IPSec, TLS, and SSL were considered relatively resource-intensive for small, low-power modules that frequently slept for extended periods. When firewalls were commonly deployed in networks, traversing them efficiently and securely was non-trivial for M2M devices.
Novelty and Inventive Step
The examiner approved the application because the prior art, whether considered alone or in combination, did not teach specific limitations of claim 1. These limitations include: (1) storing a server public key, a module identity, cryptographic algorithms, and a pre-shared secret key, where the module identity is a permanent identifier for a mobile device and the cryptographic algorithms include a symmetric ciphering algorithm; (5) sending a message to a server for a wireless network, the message comprising the module encrypted data and the corresponding module public key, wherein the server mutually derives the symmetric ciphering key using at least the module public key, and wherein the wireless network selects the pre-shared secret key for the mobile device using the module identity; and (6) authenticating the mobile device with the wireless network using a message digest with the pre-shared secret key.
Claims
This patent includes 20 claims, with claim 1 being the sole independent claim. Independent claim 1 is directed to a method for authenticating a mobile device with a wireless network using encryption and pre-shared secrets. The dependent claims generally elaborate on and refine the elements and steps of the method described in independent claim 1, providing specific details and variations.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
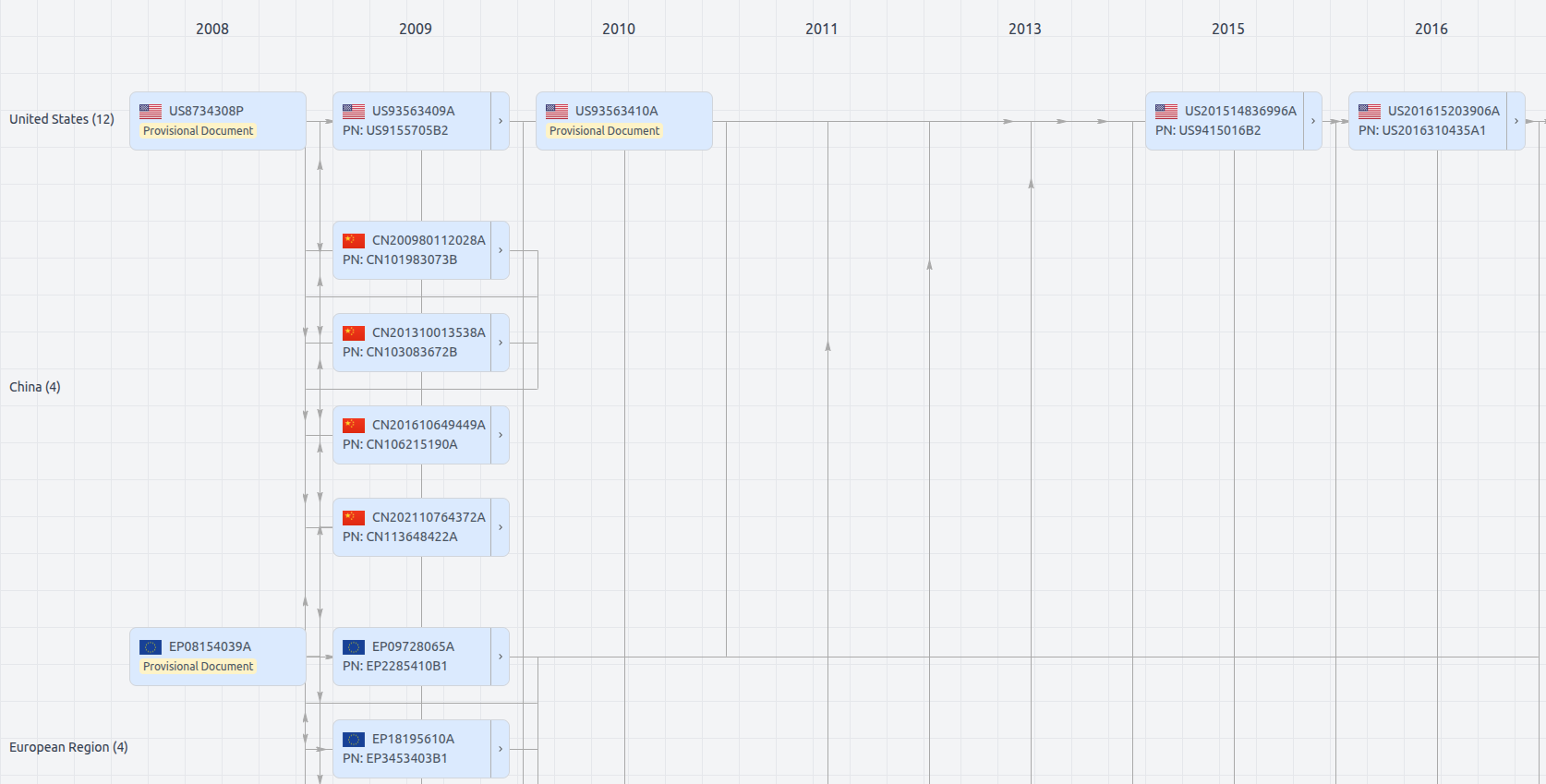
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US11973864
- Application Number
- US18111669
- Filing Date
- Feb 20, 2023
- Status
- Granted
- Expiry Date
- Oct 16, 2033
- External Links
- Slate, USPTO, Google Patents