Multi-Perimeter Firewall In The Cloud
Patent No. US12160328 (titled "Multi-Perimeter Firewall In The Cloud") was filed by Umbra Technologies Ltd on Mar 4, 2022.
What is this patent about?
’328 is related to the field of network security, specifically addressing the problem of securing traffic flowing through a global virtual network (GVN) . Traditional network security solutions, such as WAN optimizers and direct links (MPLS, DDN), often suffer from limitations in controlling traffic paths and high costs. VPNs offer privacy but lack control over traffic flow and require client-side software. The patent aims to provide a more flexible and secure solution for optimizing network traffic over standard internet connections.
The underlying idea behind ’328 is to create a multi-perimeter firewall system distributed across a virtual global network. This involves strategically placing firewalls at multiple points within the network, including cloud-based firewalls, to provide enhanced security and control over traffic flow. The key insight is that by distributing the firewall functionality and enabling communication between firewalls, the system can more effectively identify and mitigate threats while optimizing network performance.
The claims of ’328 focus on a method and system for analyzing network traffic within a virtual overlay network using multiple firewalls. Specifically, the independent claims cover receiving network traffic, analyzing it with a first firewall to determine threat information, and then transmitting that threat information to other firewalls within the network. These other firewalls then use this information to protect endpoint systems connected to the network. A key aspect is the cooperative protection of endpoint systems through the sharing of threat intelligence.
In practice, the invention involves deploying a network of firewalls, some performing stateful packet inspection (SPI) for speed and others performing deep packet inspection (DPI) for thoroughness. The firewalls communicate threat information with each other and with a central control server. This allows the system to dynamically adapt to emerging threats and optimize traffic routing. For example, a DPI firewall might identify a malicious payload and then alert SPI firewalls to block traffic from that source.
The differentiation from prior approaches lies in the distributed and collaborative nature of the firewall system. Unlike traditional perimeter firewalls, this system extends the security perimeter into the cloud and enables firewalls to learn from each other. This allows for more effective threat detection and mitigation, as well as improved network performance by offloading security processing to cloud-based resources. The system also addresses the limitations of VPNs and WAN optimizers by providing greater control over traffic paths and reducing latency.
How does this patent fit in bigger picture?
Technical landscape at the time
In the mid-2010s when ’328 was filed, network security at a time when firewalls were typically implemented at network perimeters to protect internal networks from external threats. Systems commonly relied on traditional firewall architectures, and hardware or software constraints made it non-trivial to extend firewall capabilities into cloud environments and virtualized networks.
Novelty and Inventive Step
The examiner allowed the claims because, while prior art disclosed firewalls in virtual overlay networks performing deep and stateful packet inspection, it did not disclose the specific combination of limitations recited in the claims. Specifically, the prior art failed to teach the use of threat information by other firewalls to prevent traffic from reaching a first firewall, directing traffic to a first firewall after stateful packet inspection by other firewalls, using second threat information as a reference point, and deploying a second plurality of firewalls to analyze network traffic and update configurations based on threat information from the first plurality of firewalls.
Claims
This patent contains 21 claims, with independent claims 1, 10, 11, and 13. The independent claims are generally directed to methods and systems for analyzing network traffic within a virtual overlay network using multiple firewalls to cooperatively protect endpoint systems from threats. The dependent claims generally elaborate on and refine the features of the independent claims.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
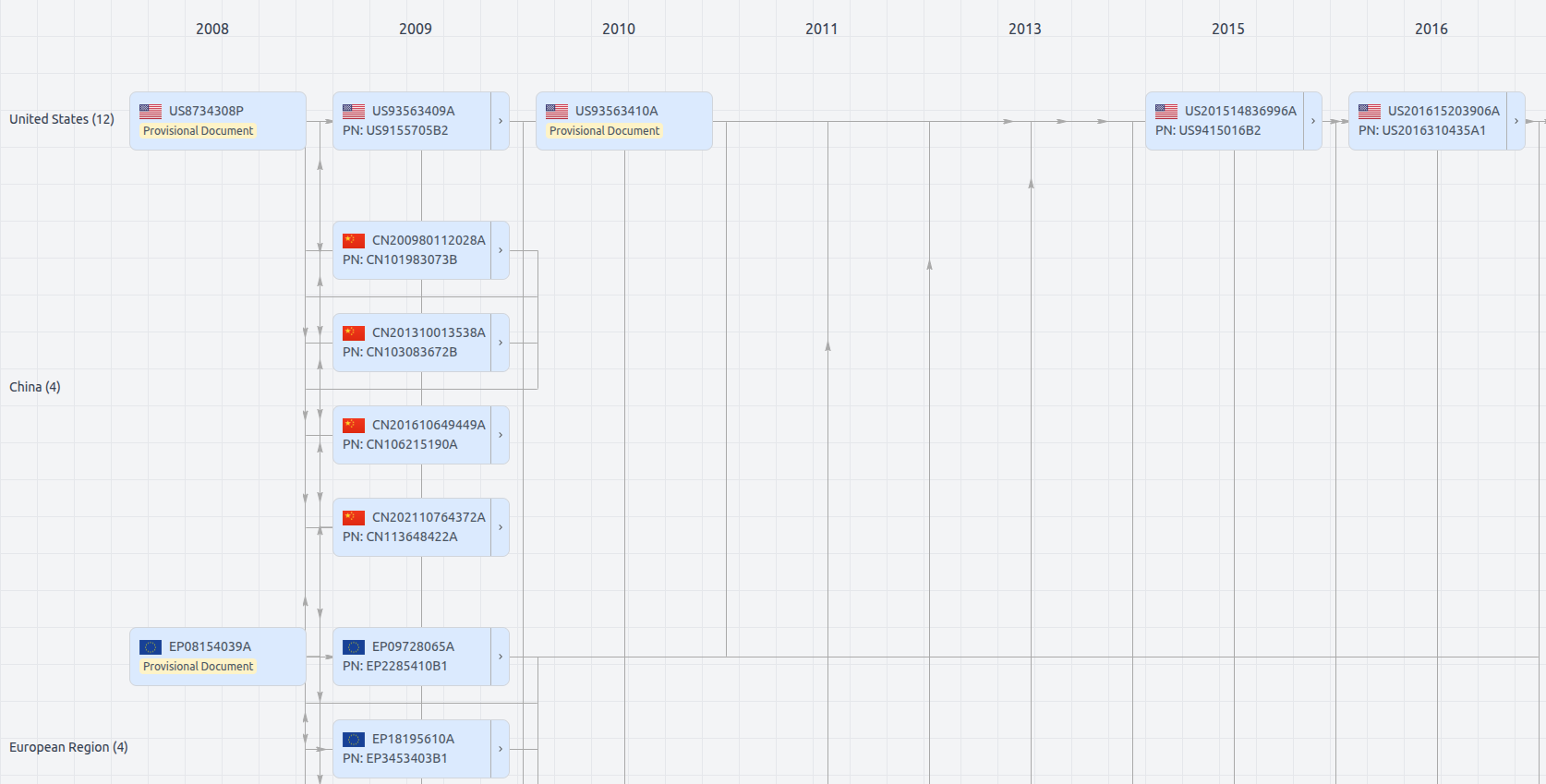
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US12160328
- Application Number
- US17686870
- Filing Date
- Mar 4, 2022
- Status
- Granted
- Expiry Date
- Apr 7, 2036
- External Links
- Slate, USPTO, Google Patents