Fraud Deterrence For Secure Transactions
Patent No. US12229768 (titled "Fraud Deterrence For Secure Transactions") was filed by Fraud Free Transactions Llc on Mar 12, 2024.
What is this patent about?
’768 is related to the field of fraud prevention in electronic transactions , particularly concerning the secure delivery and utilization of digital assets like software. The background acknowledges the increasing challenges faced by sellers due to fraudulent activities, such as stolen credit card usage, leading to financial losses and the need for robust security measures. Existing methods, like license software modules and online validation, have drawbacks including user inconvenience and susceptibility to circumvention.
The underlying idea behind ’768 is to implement a dynamic, multi-factor authentication system that adapts to the risk profile of each transaction. Instead of relying on static security measures, the system analyzes various characteristics of the request, such as the device identifier, IP address, and geographic location, to determine whether additional authentication steps are necessary. This allows for a more flexible and user-friendly approach to fraud prevention, balancing security with convenience.
The claims of ’768 focus on a non-transitory computer-readable storage medium storing instructions that, when executed, configure processors to receive a request for a software program, perform a validation analysis based on a rule set that considers device identifiers, IP addresses, and geographic locations. Based on this analysis, the system determines if multi-factor authentication (MFA) is required. If MFA is required, the user is instructed to undertake the necessary actions, and the request is fulfilled only upon successful authentication.
In practice, the invention works by first receiving a request for a digital asset, such as software. The system then analyzes the request based on a pre-defined rule set, which includes verification steps that consider factors like the device's identifier, the IP address, and the user's geographic location. The system then determines if the request meets certain conditions. If the conditions are not met, the user is prompted to undertake one or more MFA actions. Upon successful completion of these actions, the request is fulfilled, granting access to the software.
This approach differs from prior solutions by implementing a dynamic risk assessment and offering a flexible authentication process. Instead of forcing all users through the same rigid security protocols, the system adapts to the specific characteristics of each request, minimizing inconvenience for legitimate users while effectively deterring fraudulent activity. The use of multiple factors, including device identification, IP address analysis, and geographic location verification, provides a more robust defense against various types of fraud.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2000s when ’768 was filed, electronic transactions were typically implemented using client-server architectures, when systems commonly relied on username/password combinations rather than multi-factor authentication, and when hardware or software constraints made real-time risk assessment during transactions non-trivial.
Novelty and Inventive Step
The examiner allowed the claims because they recite a specific way of performing identity verification and validation that integrates a judicial exception into a practical application. The software program limits identity validation rules to a plurality of verification steps based on preselected characteristics for use in a validation analysis. This analysis includes device identifiers, IP addresses, or geographic locations, and determines whether multi-factor authentication is needed based on the verification steps and characteristics. This provides a specific improvement over prior systems, resulting in improved identity verification and validation.
Claims
This patent contains 58 claims, of which claims 1, 12, 18, 24, 31, 46, and 53 are independent. The independent claims generally focus on a non-transitory computer readable storage medium storing instructions for multi-factor authentication based on characteristics like device identifier, IP address, and geographic location. The dependent claims generally elaborate on the specifics of the characteristics, the multi-factor authentication actions, and the validation rule sets.
Key Claim Terms New
Definitions of key terms used in the patent claims.
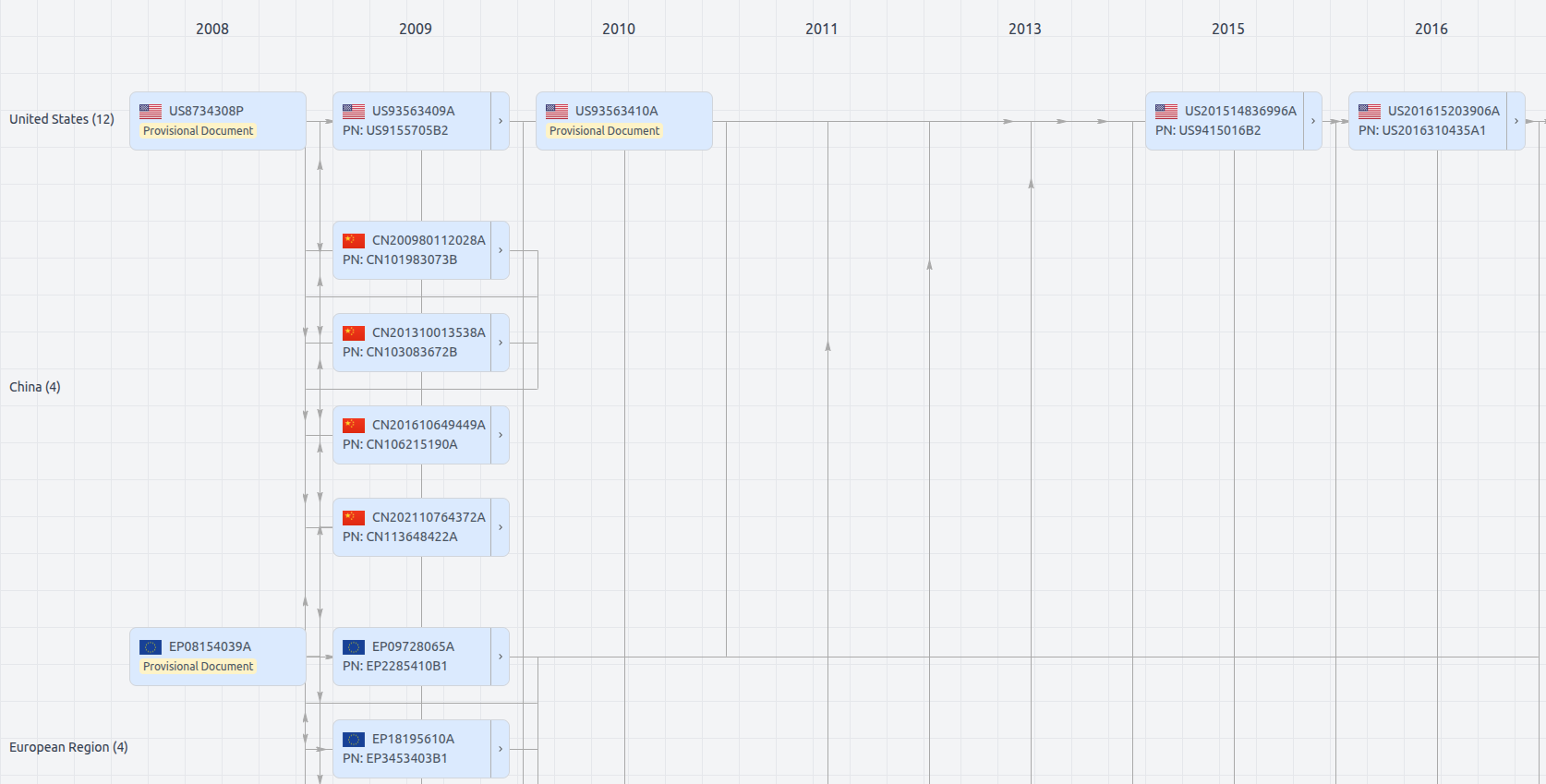
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US12229768
- Application Number
- US18602262
- Filing Date
- Mar 12, 2024
- Status
- Granted
- Expiry Date
- Jul 22, 2028
- External Links
- Slate, USPTO, Google Patents