Contextual And Risk-Based Multi-Factor Authentication
Patent No. US12231426 (titled "Contextual And Risk-Based Multi-Factor Authentication") was filed by Qomplx Llc on Sep 13, 2024.
What is this patent about?
’426 is related to the field of network security, specifically multi-factor authentication (MFA). Traditional MFA methods, while adding a layer of security beyond passwords, often rely on single points of failure, such as a compromised email account. This patent addresses the need for a more robust and dynamic authentication system that adapts to varying levels of risk and context.
The underlying idea behind ’426 is to implement a risk-based MFA system that dynamically adjusts the required level of verification based on the context of the access request. This involves monitoring network traffic, establishing a baseline of normal activity, and then requiring additional verification steps when anomalous or risky behavior is detected. The system uses a multi-dimensional time series database to store and analyze historical access data, enabling it to identify suspicious patterns.
The claims of ’426 focus on a computer system and method for authenticating a client by receiving an initial login request, storing information about the request in a time-series database, and determining if additional verification is needed. This determination is based on historical access patterns associated with the user account, specifically looking for instances where the account was previously associated with login attempts using incorrect identifiers. If such anomalies are detected, the system selects and prompts the user to complete an additional verification method.
In practice, the system monitors network traffic and user login attempts, building a profile of typical behavior. If a user attempts to log in from an unusual location, at an unusual time, or after multiple failed attempts with different usernames, the system flags the request as potentially risky. This triggers the requirement for additional verification, such as biometric scans, one-time codes, or even verification requests sent to trusted contacts. The system selects the appropriate verification method based on the level of risk and the available verification options.
’426 differentiates itself from prior MFA approaches by its dynamic and contextual nature. Instead of relying on static verification methods, it adapts to the specific circumstances of each access request. The use of a time-series database to analyze historical access patterns allows the system to detect subtle anomalies that might be missed by simpler rule-based systems. This approach provides a more secure and user-friendly authentication experience, reducing the risk of unauthorized access while minimizing disruption for legitimate users.
How does this patent fit in bigger picture?
Technical landscape at the time
In the mid-2010s when ’426 was filed, multi-factor authentication was typically implemented using methods such as one-time codes sent to mobile devices or email, or authenticator apps. At a time when network security systems commonly relied on analyzing network traffic data to detect potential security threats, determining a baseline for normal network traffic and identifying anomalies was a common practice. When hardware or software constraints made real-time analysis of large datasets non-trivial, systems often employed distributed computing techniques to handle the computational load.
Novelty and Inventive Step
The examiner allowed the claims because, while prior art systems detected emerging cyberattack behaviors on communication networks, they did not provide methods for analyzing data to reduce occurrences of low-value events and accurately identify events indicating a security breach. The claimed invention analyzes metadata to produce more actionable alerts with fewer false positives and negatives, reducing the total number of alerts while increasing their relevance to security analysts.
Claims
This patent contains 30 claims, with independent claims numbered 1, 9, 19, and 26. The independent claims generally focus on authenticating a client by receiving a request, storing information in a time-series database, and determining if additional verification is required based on historical access requests. The dependent claims generally elaborate on the specifics of the independent claims, such as processing endpoint data, using threat intelligence feeds, and providing alerts related to potential cyberattacks.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
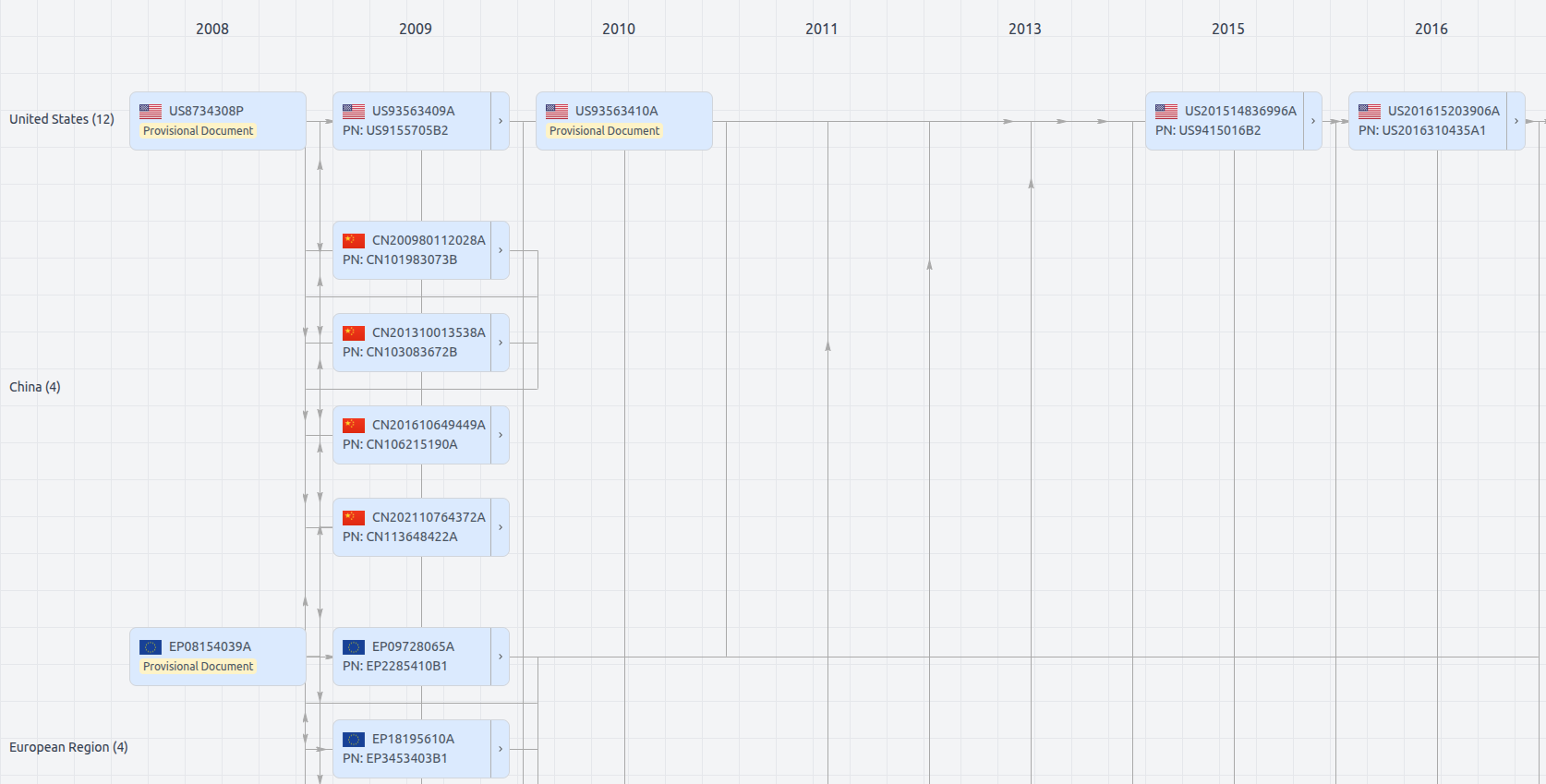
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US12231426
- Application Number
- US18885510
- Filing Date
- Sep 13, 2024
- Status
- Granted
- Expiry Date
- Oct 28, 2035
- External Links
- Slate, USPTO, Google Patents