Correlating Network Event Anomalies Using Active And Passive External Reconnaissance To Identify Attack Information
Patent No. US12301628 (titled "Correlating Network Event Anomalies Using Active And Passive External Reconnaissance To Identify Attack Information") was filed by Qomplx Llc on Sep 20, 2024.
What is this patent about?
’628 is related to the field of cybersecurity and threat analytics, specifically addressing the problem of identifying attack pathways and points of origin within a network. Existing cybersecurity rating methods often fail to adequately profile and rate organizations because they don't incorporate sufficient information about the complex relationships between network components and other organizational assets. The patent aims to improve threat detection and mitigation by correlating anomalous network events and identifying attack patterns.
The underlying idea behind ’628 is to create a cyber-physical graph that models an organization's entire infrastructure, including network devices, users, resources, and their relationships. By analyzing this graph in conjunction with real-time network event data, the system can identify anomalous events, trace their connections to other network resources, and construct a behavior graph that reveals potential attack pathways. This allows for determining the origin and progression of an attack.
The claims of ’628 focus on a computer system that stores a representation of a directed graph in hardware memory. This graph represents entities (accounts, resources) and their relationships. The system receives streaming data about network events, identifies new entities and relationships not already in the graph, and modifies the graph accordingly. For anomalous events, the system performs correlations to identify related nodes and generates a second graph representing event flows that could be involved in a cybersecurity attack, ultimately generating a report with information about these flows.
In practice, the system continuously monitors network traffic and system logs, feeding this data into the cyber-physical graph. When an unusual event occurs, such as a user accessing a restricted file or a device communicating with a known malicious IP address, the system flags it as an anomaly. It then uses the graph to trace the connections between the anomalous event and other network resources, identifying potential attack pathways. This allows security personnel to quickly understand the scope and impact of the attack.
The key differentiation from prior approaches lies in the use of a comprehensive cyber-physical graph and real-time data analysis to identify attack pathways. Instead of simply detecting individual anomalies, the system correlates these events to reveal the underlying attack patterns and points of origin. This proactive approach enables more effective threat mitigation and remediation by addressing the root causes of vulnerabilities rather than just the symptoms of an attack. The system also incorporates external threat intelligence feeds and machine learning to continuously improve its ability to detect and predict attacks.
How does this patent fit in bigger picture?
Technical landscape at the time
In the late 2010s when ’628 was filed, cybersecurity systems commonly relied on network monitoring and intrusion detection systems. At a time when threat intelligence was typically implemented using signature-based detection and rule-based correlation, hardware or software constraints made real-time analysis of large, heterogeneous datasets for anomaly detection non-trivial.
Novelty and Inventive Step
The examiner allowed the claims because the prior art, whether considered individually or in combination, did not disclose or suggest generating a representation of a second graph comprising representations of correlated nodes and edges, where these edges represent event flows that could be involved in a cybersecurity attack, and generating a report comprising information associated with these event flows. The examiner also noted that the applicant's arguments regarding other rejections were persuasive, leading to their withdrawal.
Claims
This patent contains 23 claims, with independent claims 1 and 11. The independent claims are directed to a computer system that uses graph representations and streaming data to identify and correlate events, particularly in the context of cybersecurity. The dependent claims generally elaborate on the specifics of the graph processing, event correlation, and vulnerability identification aspects of the independent claims.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
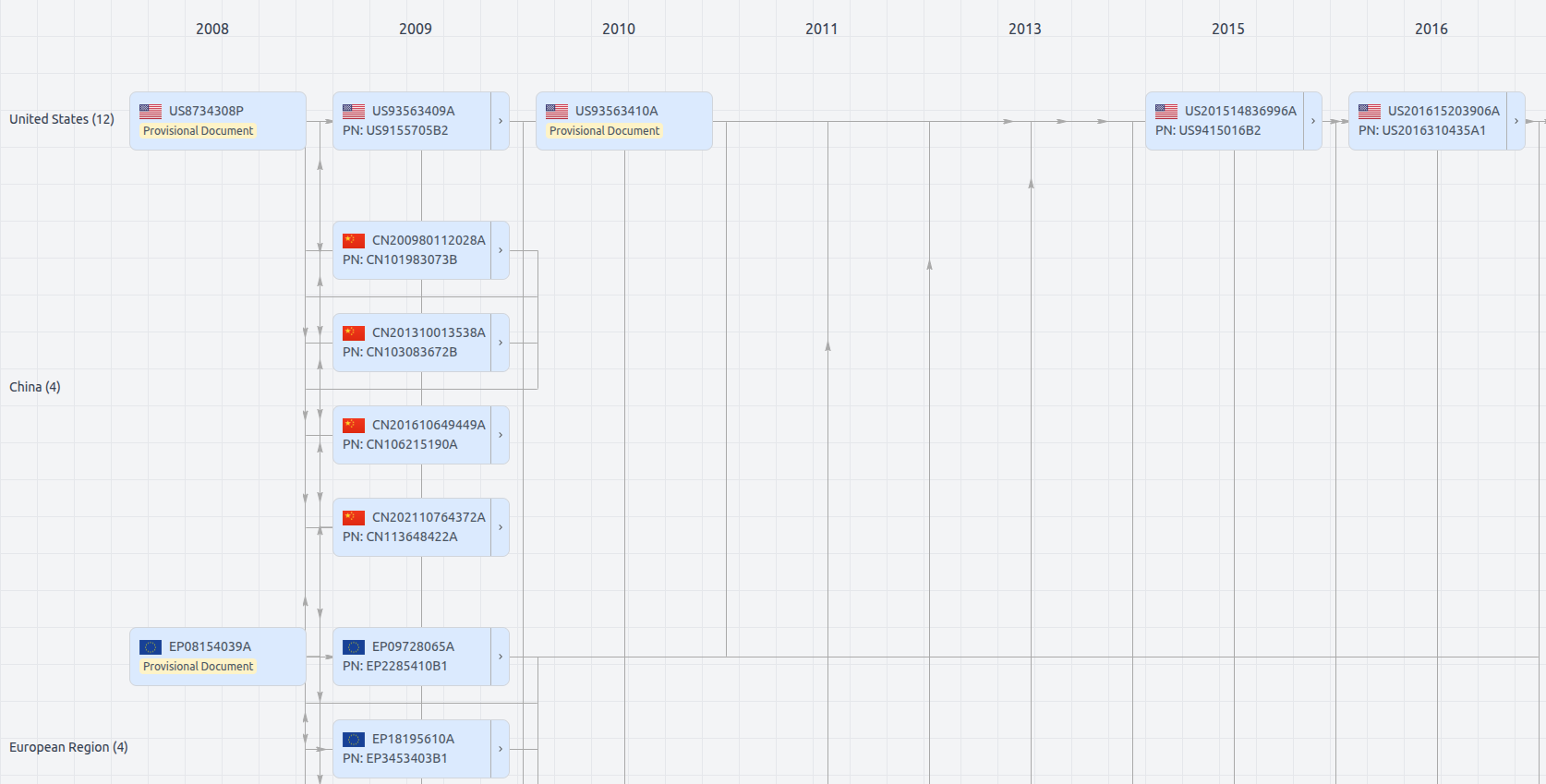
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US12301628
- Application Number
- US18892295
- Filing Date
- Sep 20, 2024
- Status
- Granted
- Expiry Date
- Oct 28, 2035
- External Links
- Slate, USPTO, Google Patents