Method And System For Forensic Data Tracking
Patent No. US12363134 (titled "Method And System For Forensic Data Tracking") was filed by Quickvault Inc on Jan 22, 2024.
What is this patent about?
’134 is related to the field of data loss prevention and forensic computing. Enterprises face increasing challenges in protecting sensitive data due to regulatory requirements and the ease with which data can leak outside authorized environments. Existing security measures like encryption and DLP tools are often insufficient, leaving a need for methods to track data movement even after it has left the protected environment.
The underlying idea behind ’134 is to embed forensic tracking mechanisms into data files, allowing their movement to be monitored across authorized and unauthorized devices and users. This involves classifying data, encoding files with tracking information, and then logging and analyzing the data's movement to identify potential breaches or policy violations. The system aims to provide visibility and control over sensitive information even after it has left the direct control of the responsible organization.
The claims of ’134 focus on receiving metadata associated with an endpoint, analyzing this metadata based on configured settings and policies, determining if the data activity deviates from normal behavior, and performing responsive actions. The deviation is determined by detecting a significant volume of metadata, relative to historical behavior, associated with a user, set of users, endpoint, or set of endpoints. The metadata includes an endpoint identifier, file name, user identifier, and data tags.
In practice, the system scans files on endpoints, classifies them based on content (e.g., presence of sensitive data patterns), and encodes them with tracking information. This encoding can involve embedding a transparent GIF with a unique URL , inserting an executable component, or encrypting the file. When the file is opened, the embedded code reports back to a central server, logging information about the endpoint and user.
This approach differs from traditional DLP solutions by focusing on post-leakage tracking . Instead of solely preventing data from leaving the protected environment, ’134 provides a mechanism to understand where the data has gone, who has accessed it, and whether any policy violations have occurred. By analyzing the logged data, the system can identify suspicious activities, generate alerts, and provide reports on data movement, enabling organizations to respond effectively to potential data breaches.
How does this patent fit in bigger picture?
Technical landscape at the time
In the early 2020s when ’134 was filed, data loss prevention was typically implemented using network-based appliances at a time when systems commonly relied on perimeter security rather than zero-trust architectures and when hardware or software constraints made comprehensive data tracking across diverse environments non-trivial.
Novelty and Inventive Step
Claims 1-30 were pending. Claims 1-4 and 6-30 were rejected for obviousness over prior art. Claims 1-30 were also rejected for nonstatutory obviousness-type double patenting. Claim 5 was indicated as allowable.
Claims
This patent contains 32 claims, of which claims 1, 19, and 32 are independent. The independent claims focus on a computing system and method for detecting deviations from normal data activity based on metadata analysis. The dependent claims generally elaborate on specific aspects, implementations, and variations of the system and method defined in the independent claims.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
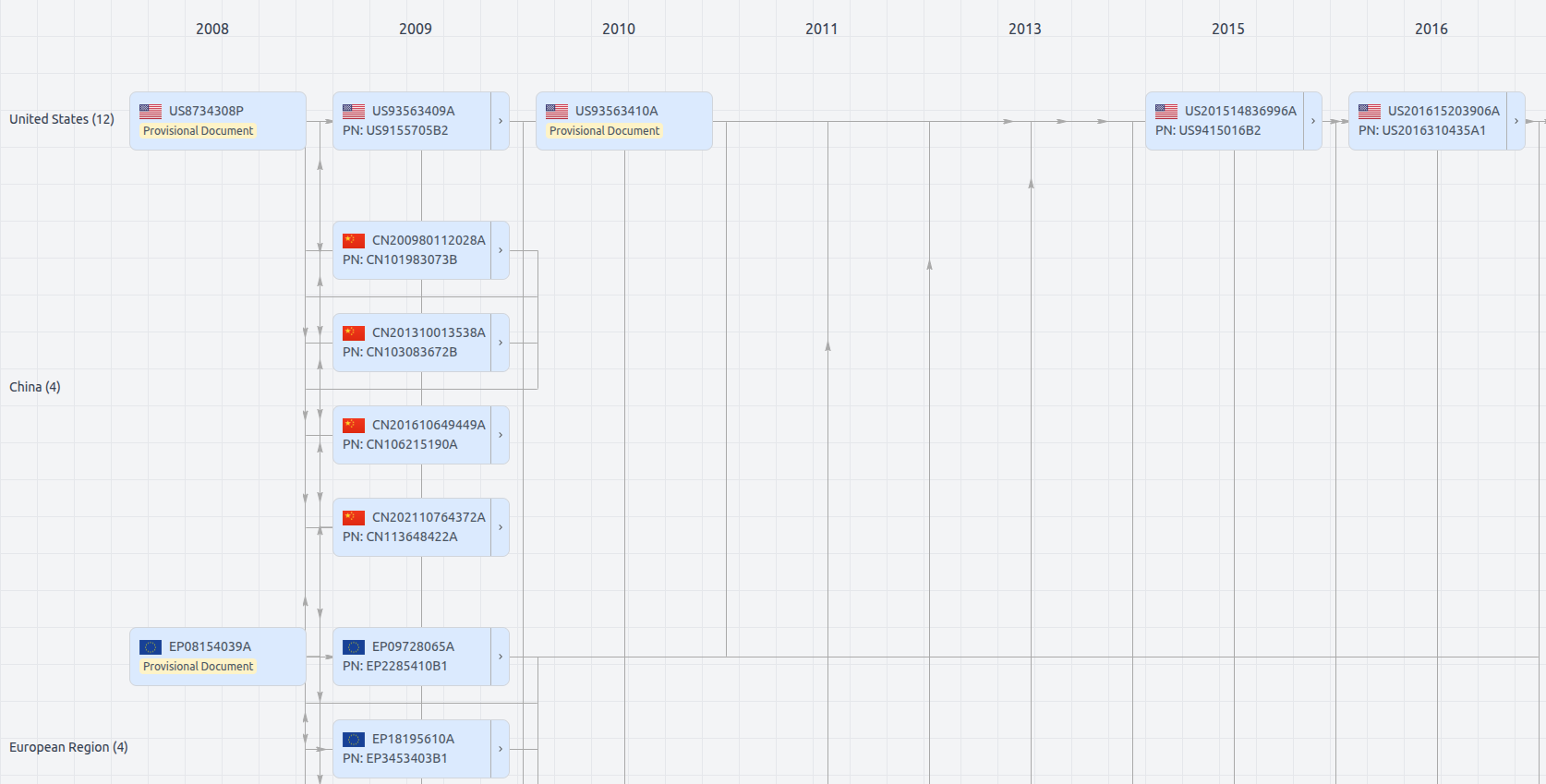
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Date
Description
Get instant alerts for new documents
US12363134
- Application Number
- US18419534
- Filing Date
- Jan 22, 2024
- Status
- Granted
- Expiry Date
- Sep 14, 2035
- External Links
- Slate, USPTO, Google Patents