Method and system for forensic data tracking
Patent No. US9565200 (titled "Method and system for forensic data tracking") on Sep 14, 2015. The application was issued on Feb 7, 2017.
What is this patent about?
'200 is related to the field of data loss prevention (DLP) and, more specifically, to systems that track the movement of data elements both within and outside of authorized enterprise environments. Traditional security measures like firewalls and encryption often fail to prevent data breaches, especially when data leaks outside protected environments via methods like USB drives or unauthorized cloud storage. Existing DLP tools have limitations, creating a need for more comprehensive data tracking and control.
The underlying idea behind '200 is to provide a system that can track data elements even after they have left the protected environment. This is achieved by classifying data based on its content, tagging it with metadata, and potentially encoding it with forensic information. The system then monitors the movement and usage of this data across various devices and users, both authorized and unauthorized, providing visibility and control over sensitive information.
The claims of '200 focus on a cloud-based forensic computing platform that receives metadata from endpoints, analyzes the data based on configured settings, determines if the data classification is appropriate for the file, and reports the results to an administrator. The platform includes components for analytics, reporting, alerts, business logic, and databases for policies, users, metadata, and settings. The endpoints have software agents capable of detecting, classifying, deleting, encrypting, and redacting data.
In practice, the invention involves scanning files on endpoints, classifying them based on their content (e.g., presence of ICD-9 codes for PHI data), and tagging them with metadata. The files can also be encoded with techniques like transparent GIFs containing URLs that report back to the cloud control server when the file is opened. This allows the system to track the file's movement even if it's copied to an unauthorized device or shared with an unauthorized user. The system can then generate alerts and reports based on the tracked data.
The invention differentiates itself from prior approaches by focusing on data provenance -- understanding the context, origin, and history of data. Unlike traditional DLP tools that primarily focus on preventing data from leaving the protected environment, this system provides visibility and control even after a breach has occurred. By encoding files with forensic information and tracking their movement, the system enables organizations to understand how data is being used and shared, even outside of their direct control, allowing for more effective incident response and compliance.
How does this patent fit in bigger picture?
Technical Landscape
In the mid-2010s when ’200 was filed, enterprise data protection was typically implemented using perimeter-based security such as firewalls and virtual private networks, or by securing access to specific applications through multi-factor authentication. At a time when systems commonly relied on static encryption for data at rest and in transit, tracking the movement of individual data elements across disparate cloud storage environments and unauthorized endpoints was difficult. Software constraints made it non-trivial to maintain data provenance once a file left a managed network, as existing data loss prevention tools generally focused on blocking transfers rather than embedding persistent forensic identifiers or tracking mechanisms within the data itself.
Prosecution Position
The examiner allowed the application because the prior art did not teach a forensic computing platform that utilizes a specific type of deployed software agent on an endpoint. While previous systems could log file metadata and analyze data movement, the examiner noted that the prior art failed to disclose an agent equipped with integrated modules designed to simultaneously detect, classify, delete, encrypt, and redact data stored on the endpoint. Furthermore, the examiner found that the prior art did not describe using data element tags that include specific indicators for data fields or types within a file in the manner claimed.
Claims
There are 18 claims in total, with claim 1 being the only independent claim. The independent claim focuses on a forensic computing platform deployed as a cloud control server with an endpoint software agent that analyzes files and reports data classification issues. The dependent claims generally elaborate on the components, steps, and functionalities of the forensic computing platform and its software agent, further defining the elements and actions described in the independent claim.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
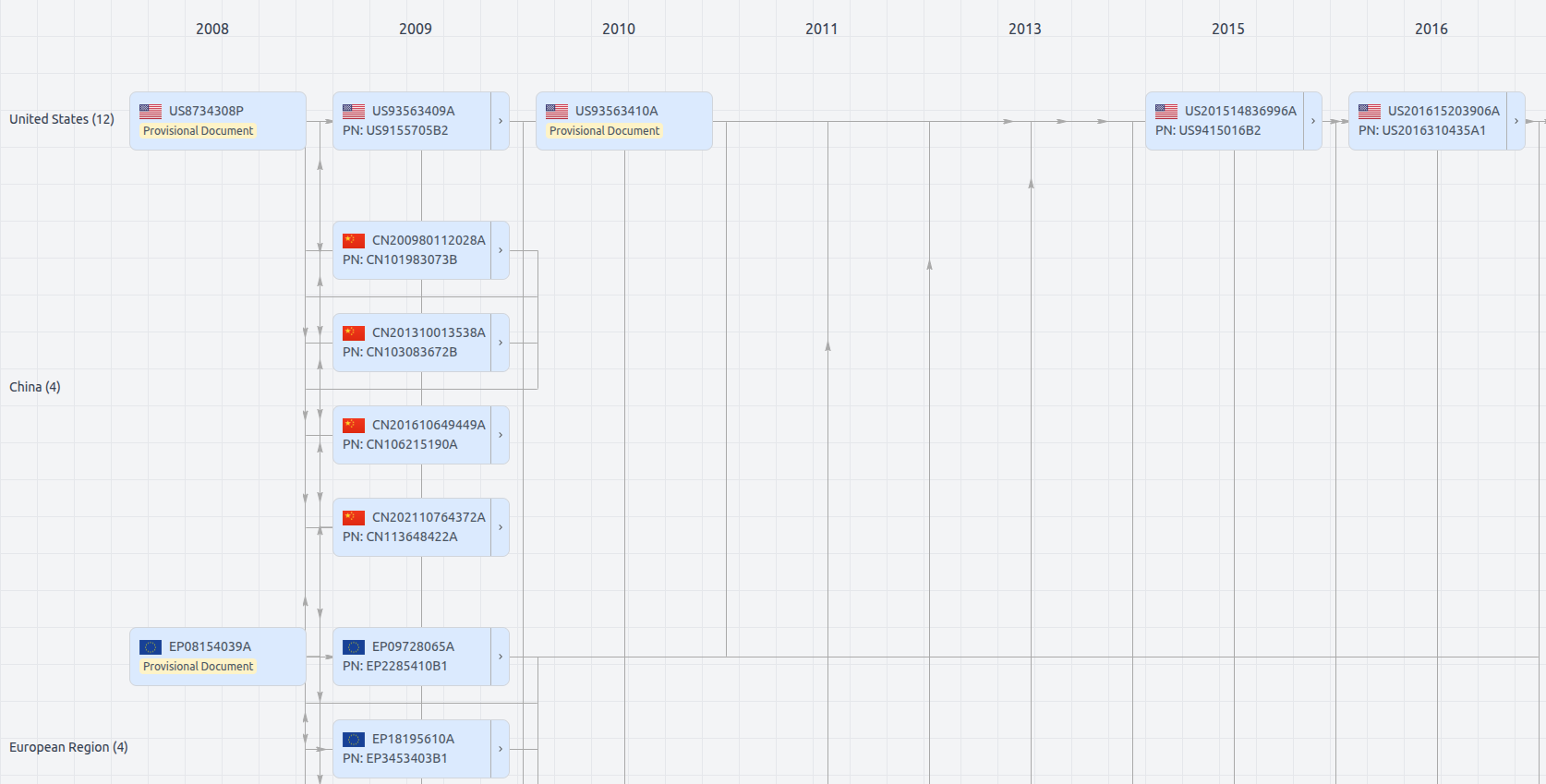
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Get instant alerts for new documents
US9565200
- Application Number
- US14853464A
- Filing Date
- Sep 14, 2015
- Publication Date
- Feb 7, 2017
- External Links
- Slate, USPTO, Google Patents