Method and system for forensic data tracking
Patent No. US9961092 (titled "Method and system for forensic data tracking") on Jan 15, 2017. The application was issued on May 1, 2018.
What is this patent about?
'092 is related to the field of data loss prevention (DLP) and, more specifically, to systems that track the movement and usage of data elements across authorized and unauthorized devices and users. Traditional DLP solutions often fail to prevent all data leakage, leaving sensitive data vulnerable once it escapes the protected environment. This patent addresses the need for a more comprehensive method to maintain visibility, auditability, and control over sensitive information, even after it leaves the direct control of an organization.
The underlying idea behind '092 is to embed forensic tracking mechanisms directly into data files, allowing their movement and usage to be monitored even outside of authorized environments. This is achieved by classifying data based on its content, encoding it with tracking information, and then logging its activity as it is accessed and shared. The system can then use this information to identify potential data breaches, policy violations, and other security risks.
The claims of '092 focus on a cloud-based forensic computing platform that receives metadata from endpoints, analyzes the data based on configured settings and criteria, determines if the data classification is inappropriate for the file on the endpoint, and then remediates the file by encrypting, deleting, or redacting the data. The platform uses data element tags to identify sensitive information within files and determine the appropriate data classification.
In practice, the invention involves scanning data files on endpoints, classifying them according to a data classification policy, and tagging them with metadata. The files can then be encoded with tracking information, such as a transparent GIF with an embedded URL, or by encrypting the file and requiring a decryption key from the cloud server. When the file is accessed, the tracking information reports back to the cloud control server, providing details about the file's location, user, and other relevant information. The system can then use this information to generate alerts, reports, and other insights.
This approach differs from traditional DLP solutions by focusing on data provenance and tracking data even after it has left the protected environment. Instead of simply preventing data from leaving the network, this invention provides a mechanism to monitor and control data throughout its lifecycle, regardless of where it is stored or who is accessing it. This allows organizations to maintain visibility and control over their sensitive information, even in the face of data breaches and other security incidents.
How does this patent fit in bigger picture?
Technical Landscape
In the mid-2010s when ’092 was filed, enterprise data security was typically implemented using perimeter-based defenses such as firewalls and virtual private networks at a time when systems commonly relied on static encryption for data at rest and in transit rather than persistent tracking of individual data elements. During this era, software constraints made the granular monitoring of data provenance non-trivial when files moved between authorized managed endpoints and unmanaged cloud storage services or external devices. Engineering practices for data loss prevention often focused on blocking transfers at the gateway, as maintaining visibility into the movement and modification of sensitive information across disparate administrative domains remained a significant technical challenge.
Prosecution Position
Following the filing of this application, the applicant filed a preliminary amendment that canceled the original claims and introduced new claims 21-38. The examiner subsequently issued a non-final office action rejecting these claims on the ground of nonstatutory double patenting. However, the prosecution record explicitly indicates that claims 21-38 were found to be allowable over the cited prior art. The application later proceeded toward allowance as a procedural fact, though the prosecution record does not describe the specific technical reasoning or claim changes that led to this outcome.
Claims
This patent contains 18 claims, with claim 1 being independent. Independent claim 1 is directed to a forensic computing platform deployed as a cloud control server with endpoints and software agents for detecting, classifying, and remediating data. The dependent claims generally elaborate on the components, steps, and functionalities of the forensic computing platform described in the independent claim.
Key Claim Terms New
Definitions of key terms used in the patent claims.
Litigation Cases New
US Latest litigation cases involving this patent.
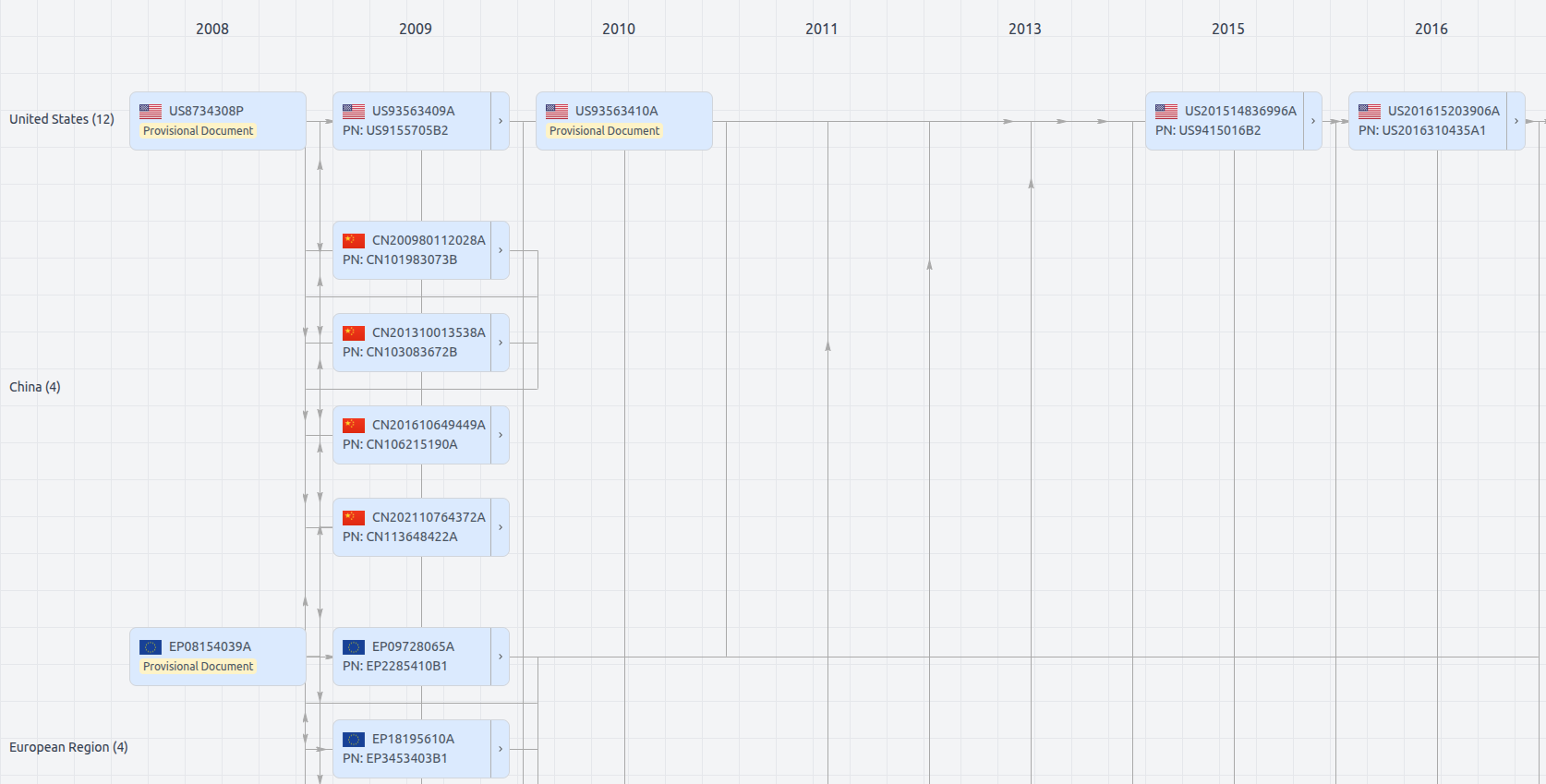
Patent Family
File Wrapper
The dossier documents provide a comprehensive record of the patent's prosecution history - including filings, correspondence, and decisions made by patent offices - and are crucial for understanding the patent's legal journey and any challenges it may have faced during examination.
Get instant alerts for new documents
US9961092
- Application Number
- US15406746A
- Filing Date
- Jan 15, 2017
- Publication Date
- May 1, 2018
- External Links
- Slate, USPTO, Google Patents